CVE-2024-4040: CrushFTP Virtual File System (VFS) Sandbox Escape Vulnerability Exploited

A zero-day vulnerability in CrushFTP was exploited in the wild against multiple U.S. entities prior to fixed versions becoming available as the vendor recommends customers upgrade as soon as possible.
Background
On April 19, CrushFTP published an advisory for a zero-day vulnerability in its file transfer tool which bears the same name.
| CVE | Description | CVSSv3 | Severity |
|---|---|---|---|
| CVE-2024-4040 | CrushFTP VFS Sandbox Escape Vulnerability | 7.7 | High |
No CVE identifier was initially assigned for this vulnerability. However, on April 22, h4sh, a security engineer and founder of DirectCyber, an Australian Cyber Security Incident Response Team (CSIRT), assigned a CVE for this flaw.
Analysis
CVE-2024-4040 is an improper input validation vulnerability in CrushFTP. An authenticated attacker with low privileges could exploit this vulnerability on a vulnerable CrushFTP server to escape the virtual file system (VFS) sandbox. Successful exploitation would allow an attacker to download system files.
Zero-day exploitation of VFS sandbox escape flaw
According to researchers at CrowdStrike, CVE-2024-4040 has been exploited in the wild as a zero-day. Specifically, its report notes that these attacks are targeted in nature and that intrusions have been discovered at “multiple U.S. entities” with a focus on “intelligence-gathering” that is “possibly politically motivated.” No further details about attribution of these targeted attacks are available as of April 23.
Attackers are probing for vulnerable CrushFTP servers
In a statement to The Record, an official from CrushFTP says that they have seen “a customer who was already patched who was probed for the vulnerability” adding that if the patch had not been applied “important config info would have been stolen.” This official stressed that customers “need to update ASAP.”
Over 7,100 CrushFTP servers publicly accessible and potentially vulnerable
Based on a shodan query in a Nuclei template created by h4sh to identify potentially vulnerable CrushFTP servers, there are reportedly over 7,100 CrushFTP servers publicly accessible. It is unclear how many of these systems are potentially vulnerable.
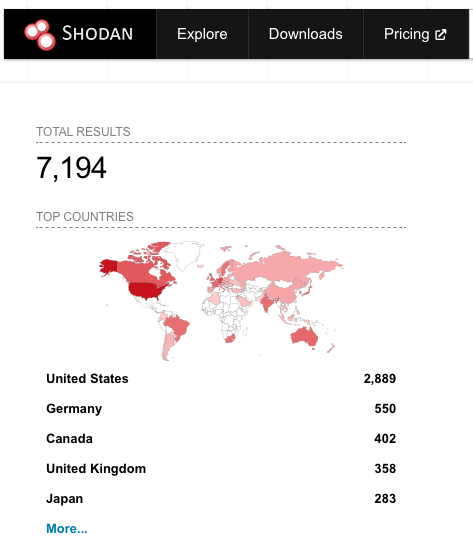
Shodan query results as of April 22 for publicly accessible CrushFTP servers
Proof of concept
On April 23, a public proof-of-concept (PoC) for this vulnerability was posted to GitHub. It was created by Simon Garrelou of Airbus Community Emergency Response Team (CERT), who is credited with discovering and reporting CVE-2024-4040 to CrushFTP.
Additionally, it is important to highlight that it is common practice for attackers to seed fake PoCs on public source code repositories like GitHub in an effort to target both researchers and would-be attackers looking for exploit code. In the case of CVE-2024-4040, we’ve seen a repository published to GitHub directing users to a third-party site called SatoshiDisk that requests a payment of 0.00735 Bitcoin ($513.30 USD as of April 22).
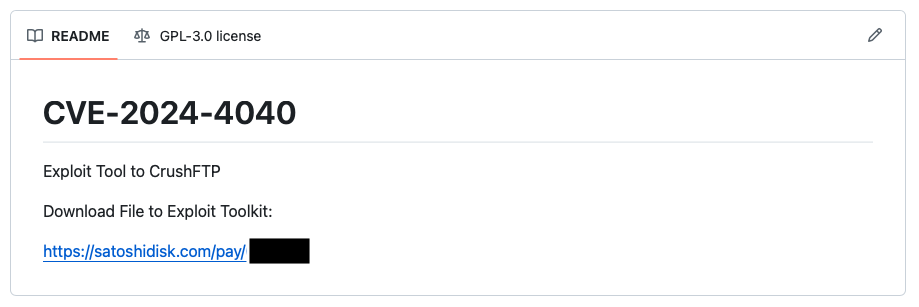
Example repository on GitHub seeking Bitcoin payment for a fake exploit for CVE-2024-4040
It is unlikely that the exploit code will work and we do not expect it to be malicious in nature. Instead, it is more likely that the attackers are seeking to make money from the interest in the exploit code for this vulnerability.
Solution
On April 23, CrushFTP released fixes for version 10 and version 11 of CrushFTP:
| Affected Versions | Fixed Version |
|---|---|
| 11.0.1 | 11.1.0 |
| 10.0.0 through 10.6.1 | 10.7.1 |
| Below 10.0.0 | Upgrade to 11.1.0 |
Previously, reports suggested that if CrushFTP was behind a demilitarized zone (DMZ) then users would be protected against this flaw. However, as of April 22, CrushFTP disputed this claim, noting that a DMZ “does not fully protect you.” Customers using a vulnerable version of CrushFTP are advised to update to a fixed version as soon as possible.
Garrelou also developed a script to scan CrushFTP logs to search for potential indicators of compromise.
Identifying affected systems
A list of Tenable plugins for this vulnerability can be found on the individual CVE page for CVE-2024-4040 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
Get more information
- CrushFTP Wiki Page for CrushFTP 11 (Advisory)
- SITUATIONAL AWARENESS // 2024-04-19 // CrushFTP Virtual Filesystem Escape Vulnerability in the Wild
- The Record News: CrushFTP urges customers to patch file transfer tool ‘ASAP’
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Related Articles
- Exposure Management
- Vulnerability Management
- Exposure Management






