Tenable
Identity Exposure
The essential solution for
the identity-intelligent enterprise
Unleash a new level of end-to-end protection from identity-based attacks.

Stop identity-based exploits
Know
your identity
reality
Collapse enterprise silos and unify identities across Active Directory, hybrid and Entra ID.
Expose
your top identity
gaps
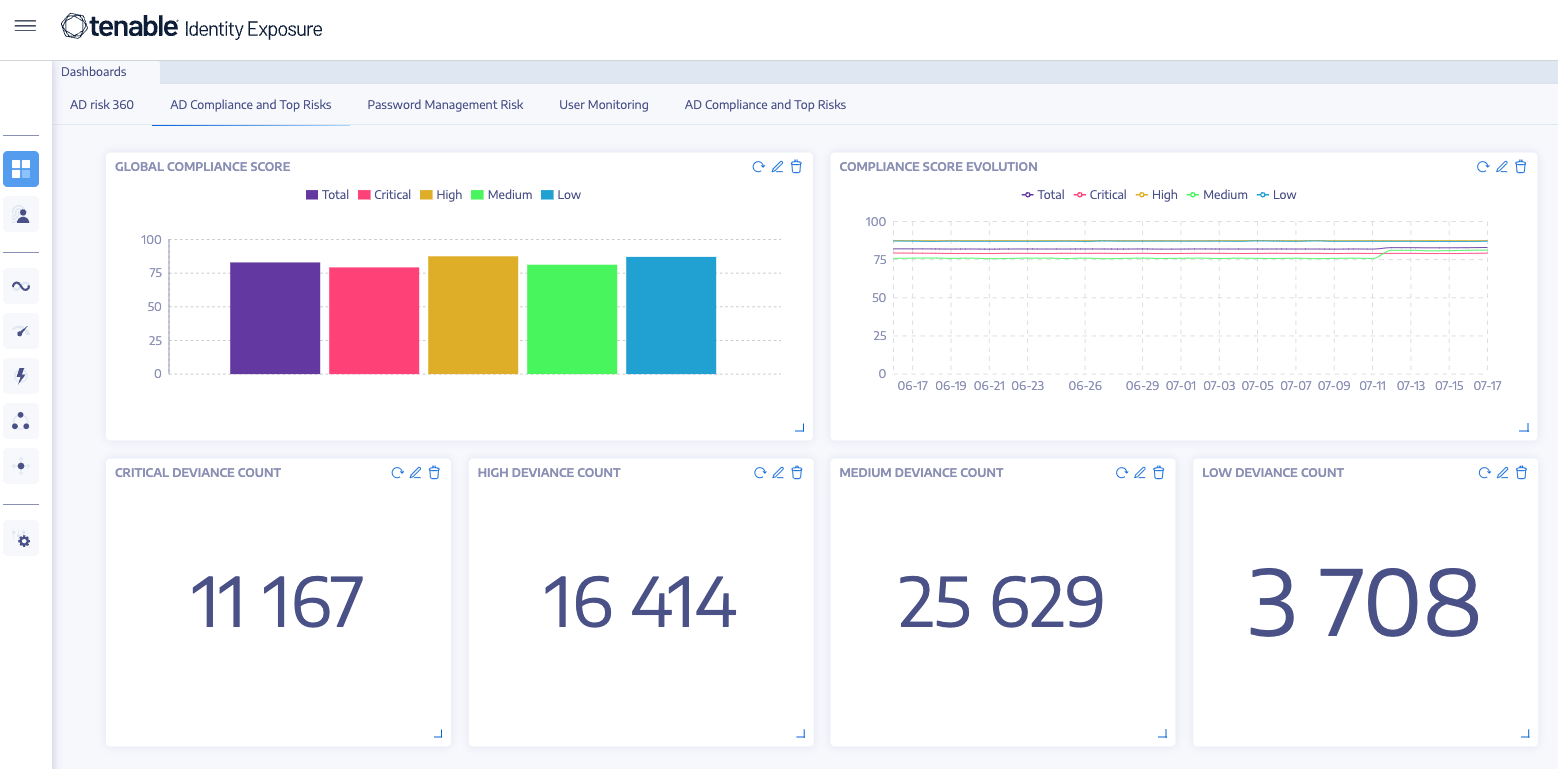
Evaluate your identities using risk scoring to locate your riskiest ones that require attention.
Close identity-based exposures quickly
Use step-by-step prioritization to rapidly close security gaps with the highest likelihood of identity-based exploits.
Close identity exposure to reduce risk
Identities are the new perimeter—compromised identities are at the center of nearly every successful cyberattack. By exposing and closing the security gaps where identity-based exploits thrive, Tenable Identity Exposure strengthens your security posture and confidently prevents attacks before they occur.
See what matters
Tenable Identity Exposure continuously validates your Active Directory and Entra ID environments for weaknesses, misconfigurations and activity that can lead to damaging attacks. Integrating deep identity context into the Tenable One Exposure Management Platform can further help you see risky toxic combinations while dramatically improving prioritization and efficiency to remediate exposure that matters most to the organization.
Eliminate attack paths
Tenable Identity Exposure eliminates the exposures and attack paths bad actors might otherwise exploit, ensuring attackers struggle to find a foothold and have no next step if they do.
Initial
foothold
Via phishing or vulnerability
Explore
Lateral movement across the target environment
Elevate
Gain privileged access
Evade
Hide forensic footprints
Establish
Install code for permanence
Exfiltrate
Exfiltrate data or hold target to ransom
Secure Active Directory
- Discover underlying issues threatening your Active Directory security
- Identify dangerous trust relationships
- Use Identity Risk Scoring to rank each identity by level of risk to the environment
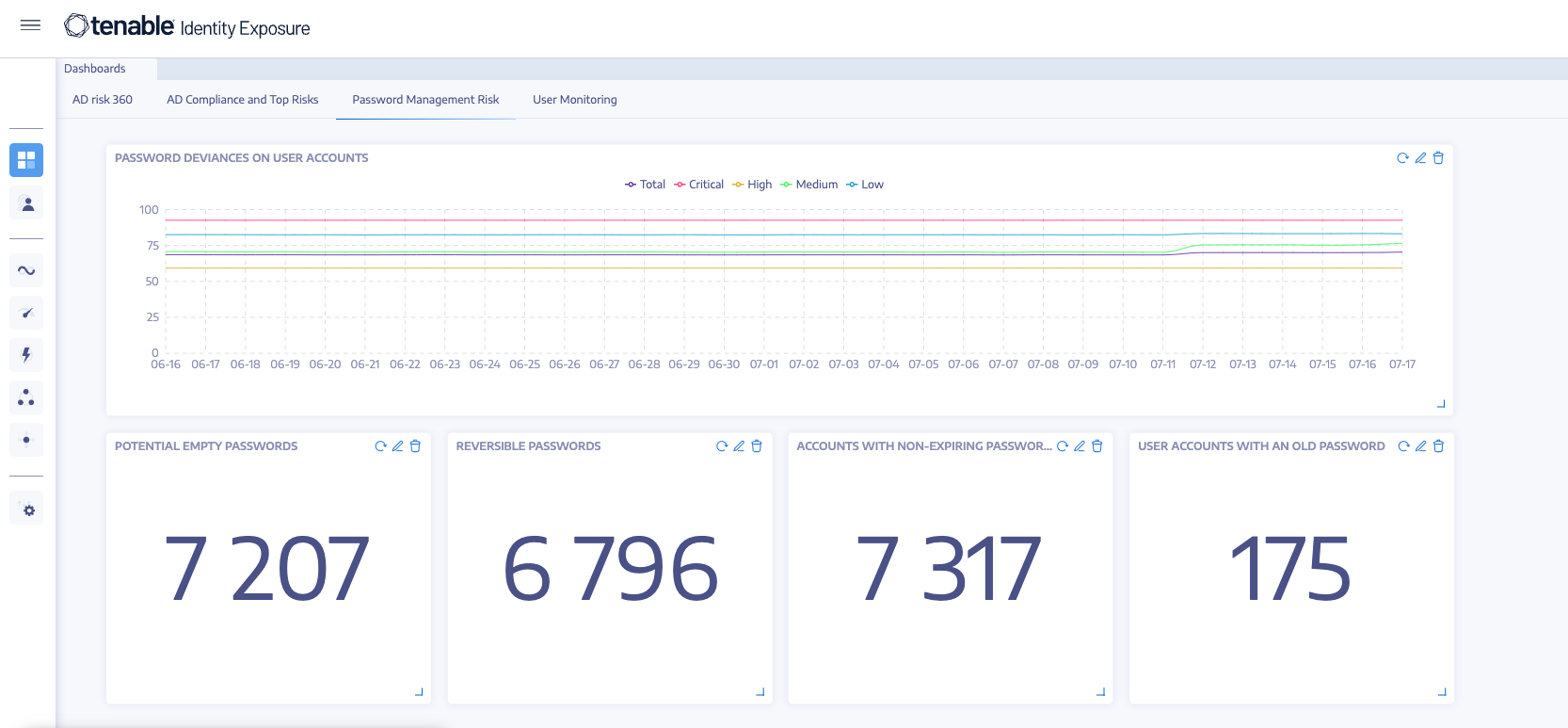
- Boost your organization’s password hygiene and slash the risk of password-related attacks
- Catch every change in your Active Directory and Entra ID
- Make the link between Active Directory changes and malicious actions and detect AD attacks in real-time
- Prioritize remediation steps to focus on the riskiest identities and misconfigurations first
- Unify identities in Active Directory and Entra ID
- Visualize in-depth attack details
- Explore MITRE ATT&CK descriptions directly from incident details
Confidently prevent attacks before they occur
Deployed anywhere
Supporting both Active Directory and Entra ID, Tenable Identity Exposure provides flexible architectural designs: on-prem to keep your data on-site and under your control and SaaS to leverage the cloud.

No delays
Prevents and detects sophisticated Active Directory attacks without agents and privileges, requiring only a standard user account for auditing of configurations and the identification of attacks against Active Directory.

Available through Tenable One: The world’s only AI-powered exposure management platform
Tenable One solves the central challenge of modern security: a deeply divided approach to seeing and doing battle against cyber risk. We remove risk by unifying security visibility, insight and action across the attack surface to rapidly expose and close gaps. Customers use Tenable One to eradicate priority cyber weaknesses and protect against attacks—from IT infrastructure to cloud environments to critical infrastructure and everywhere in between.
Learn more
FAQs
- What are the main capabilities of Tenable Identity Exposure?
-
Tenable Identity Exposure enables you to detect and respond to attacks in real time and find and fix weaknesses in Active Directory before attackers exploit them. The main capabilities of Tenable Identity Exposure are:
- Uncover any hidden weaknesses within your Active Directory configurations
- Discover underlying issues threatening your Active Directory security
- Dissect each misconfiguration – in simple terms
- New Identity Risk scoring capability quantifies asset risk by combining vulnerability, exposure and identity entitlements (powered by Tenable’s Artificial Intelligence and Data Science Engine)
- Get recommended fixes for each issue
- Create custom dashboards to manage your Active Directory security to drive risk reduction
- Discover dangerous trust relationships
- New View Unified Identities from Active Directory and Entra ID
- Catch every change in your AD
- Uncover major attacks per domain in your Active Directory
- Visualize every threat from an accurate attack timeline
- Consolidate attack distribution in a single view
- Make the link between Active Directory changes and malicious actions
- Analyze in-depth details of an Active Directory attack
- Explore MITRE ATT&CK ® descriptions directly from detected incidents
- Which Active Directory attacks and techniques does Tenable Identity Exposure detect?
-
Tenable Identity Exposure detects many of the techniques used in cyber attacks to gain elevated privileges and enable lateral movement, including DCShadow, Brute Force, Password Spraying, DCSync, Golden Ticket and more.
- Which privilege attack vectors on Active Directory does Tenable Identity Exposure identify?
-
Tenable Identity Exposure has an extensive library of known attack vectors that attackers use to gain privilege. These include:
Attack Vector
Description
Known Offensive tools
Mitre Attack Matrix
Privileged accounts running Kerberos services
Highly privileged accounts using a brute-forceable Kerberos Service Principal Name
Kerberom
Privilege Escalation, Lateral movement, Persistence
Dangerous Kerberos delegation
Check that no dangerous delegation (unconstrained, protocol transition, etc.) is authorized
Nishang
Privilege Escalation, Lateral movement, Persistence
Use of weak cryptography algorithms into Active Directory PKI
Root certificates deployed on internal Active Directory PKI must not use weak cryptographic algorithms
ANSSI-ADCP
Persistence, Privilege escalation, Lateral movement
Dangerous access rights delegation on critical objects
Some access rights allowing illegitimate users to control critical objects have been found
BloodHound
Exfiltration, Lateral movement, Command and control, Credential access, Privilege escalation
Multiple issues in the password policy
On some specific accounts, the current password policies are insufficient to ensure robust credentials protection
Patator
Defense evasion, Lateral movement, Credential access, Privilege escalation
Dangerous RODC management accounts
The administrative groups in charge of Read-Only Domain Controllers contain abnormal accounts
Impacket
Credential access, Defense evasion, Privilege escalation
Sensitive GPO linked to critical objects
Some GPO managed by non-administrative accounts are linked to sensitive Active Directory objects (e.g. the KDC account, Domain Controllers, administrative groups, etc.)
ANSSI-ADCP
Command and control, Credential access, Persistence, Privilege escalation
Administrative accounts allowed to connect to other systems than the Domain Controllers
The security policies deployed on the monitored infrastructure does not prevent administrative accounts to connect to resources other than DC, leading to sensitive credentials exposure
CrackMapExec
Defense evasion, Credential access
Dangerous trust relationship
Misconfigured trust relationship attributes decrease the security of a directory infrastructure
Kekeo
Lateral movement, Credential access, Privilege escalation, Defense evasion
Reversible passwords in GPO
Verify that no GPO contain passwords stored in a reversible format
SMB Password crawler
Credential access, Privilege escalation
Computers running an obsolete OS
Obsolete systems are not supported by the editor anymore and greatly increase the infrastructure vulnerability
Metasploit
Lateral movement, Command and control
Accounts using a pre-Windows 2000 compatible access control
Account member of the pre-Windows 2000 Compatible Access Group can bypass specific security measures
Impacket
Lateral movement, Defense evasion
Local administrative account management
Ensure local administrative accounts are managed centrally and securely using LAPS
CrackMapExec
Defense evasion, Credential access, Lateral movement
Dangerous anonymous users configuration
Anonymous access is activated on the monitored Active Directory infrastructure leading to sensitive information leak
Impacket
Exfiltration
Abnormal RODC filtered attributes
The filtering policies applied on some Read-Only Domain Controllers can lead to sensitive information caching, allowing privilege escalations
Mimikatz (DCShadow)
Privilege escalation, Defense evasion
Lacking restriction on lateral movements attack scenario
Lateral movement restriction has not been activated on the monitored Active Directory infrastructure, allowing attackers to bounce from machine to machine with the same level of privileges
CrackMapExec
Lateral movement
Clear-text password stored in DC shares
Some files on DC shares, accessible by any authenticated user, are likely to contain clear-text password, allowing privilege escalation
SMBSpider
Credential access, Privilege escalation, Persistence
Dangerous access control rights on logon scripts
Some scripts, run during a computer or a user logon, have dangerous access rights, leading to privilege escalation
Metasploit
Lateral movement, Privilege escalation, Persistence
Dangerous parameters are used in GPO
Some dangerous parameters (e.g. restricted groups, LM hash computation, NTLM authentication level, sensitive parameters, etc.) are set by GPO, creating security breaches
Responder
Discovery, Credential access, Execution, Persistence, Privilege escalation, Defense evasion
Dangerous parameters defined in the User Account Control configuration
The User Account Control attribute of some user accounts defines dangerous parameters (e.g. PASSWD_NOTREQD or PARTIAL_SECRETS_ACCOUNT)PARTIAL_SECRETS_
ACCOUNT), which endanger the security of said accountMimikatz (LSADump)
Persistence, Privilege escalation, Defense evasion
Lacking application of security patches
Some server registered in Active Directory did not recently apply security updates
Metasploit
Command and control Privilege escalation, Defense evasion
Brute force attempt on user accounts
Some user accounts have been targeted by a brute force attempt
Patator
Credential access
Kerberos configuration on user account
Some accounts are using weak Kerberos configuration
Mimikatz (Silver Ticket)
Credential access, Privilege escalation
Abnormal share or file stored on the DC
Some domain controllers are used to host non-necessary files or network shares
SMBSpider
Discovery, Exfiltration
- Which backdooring techniques on Active Directory does Tenable Identity Exposure identify?
-
Tenable Identity Exposure has an extensive library of known backdooring techniques that attackers use to gain persistence. These include:
Backdooring technique
Description
Known Offensive tools
Mitre attack Matrix
Ensure SDProp consistency
Control that the adminSDHolder object is in a clean state
Mimikatz (Golden Ticket)
Privilege escalation, Persistence
Ensure SDProp consistency
Verify that users’ primary group has not been changed
BloodHound
Privilege escalation, Persistence
Verify root domain object permissions
Ensure the permissions set on the root domain object are sane
BloodHound
Privilege escalation, Persistence
Verify sensitive GPO objects and files permissions
Ensure that permissions set on the GPO objects and files linked to sensitive containers (like the Domain Controllers OU) are sane
BloodHound
Execution, Privilege escalation, Persistence
Dangerous access rights on RODC KDC account
The KDC account used on some Read-Only Domain Controllers can be controlled by illegitimate user account, leading to credential leaks
Mimikatz (DCSync)
Privilege escalation, Persistence
Sensitive certificates mapped to user accounts
Some X509 certificates are stored in the altSecurityIdentities user account attribute, allowing certificate’s private key owner to authenticate as this user
Command and control, Credential access, Privilege escalation, Persistence
Rogue Krbtgt SPN set on regular account
The Service Principal Name of the KDC is present on some regular user account, leading to Kerberos tickets forgery
Mimikatz (Golden Ticket)
Privilege escalation, Persistence
KDC password last change
KDC account password must be changed regularly
Mimikatz (Golden Ticket)
Credential access, Privilege escalation, Persistence
Accounts having a dangerous SID History attribute
Check user or computer accounts using a privileged SID in SID history attribute
DeathStar
Privilege escalation, Persistence
Rogue domain controllers
Ensure only legitimate Domain controller servers are registered into Active Directory infrastructure
Mimikatz (DCShadow)
Execution, Defense evasion, Privilege escalation, Persistence
Illegitimate Bitlocker key access control
Some Bitlocker recovery keys stored in Active Directory can be accessed by other people than administrators and linked computers
ANSSI-ADCP
Credential access, Privilege escalation, Persistence
Abnormal entries in the Schema security descriptor
The Active Directory Schema has been modified leading to new standard access rights or objects that can endanger the monitored infrastructure
BloodHound
Privilege escalation, Persistence
DSRM account activated
The Active Directory recovery account has been activated, exposing it to credential theft
Mimikatz (LSADump)
Credential access, Execution, Defense evasion, Privilege escalation, Persistence
Authentication hash not renewed when using smartcard
Some user accounts using smartcard authentication do not renew their credentials hash frequently enough
Mimikatz (LSADump)
Persistence
Reversible passwords for User accounts
Verify no parameter make passwords stored in a reversible format
Mimikatz (DC Sync)
Credential access
Use of explicit denied access on containers
Some Active Directory containers or OUs define explicit denied access, leading to potential backdoor concealment
BloodHound
Defense evasion, Persistence
- How does Tenable Identity Exposure audit Active Directory?
-
Tenable Identity Exposure is the only solution on the market that does not need any deployment on Domain Controllers nor endpoints. Furthermore, Tenable Identity Exposure only needs user-level privileges to operate. This unique architecture enables security teams to rapidly audit the configuration of Active Directory without complex deployment issues.
- Is Tenable Identity Exposure a point-in-time security audit tool for Active Directory?
-
AD misconfigurations happen all the time, so that point-in-time audits become deprecated only minutes after they start and focus on misconfigurations rather than including indicators of compromise.
On the other hand, Tenable Identity Exposure is a security platform that continuously scans your AD for new weaknesses and attacks - alerting users in real-time to issues.
- Can Tenable Identity Exposure detect Golden Ticket attacks?
-
Yes, Golden Ticket is one of the many attack techniques that Tenable Identity Exposure can detect and help you prevent. With hundreds of security checks and correlations running in parallel, Tenable Identity Exposure has the widest security scope available for AD.
- Does Tenable Identity Exposure integrate with my SIEM / SOAR / ticketing system / etc.?
-
AD security is an important piece of your security puzzle, and Tenable Identity Exposure blends into your security ecosystem seamlessly.
Our Syslog integration ensures that all SIEM and most ticketing systems can integrate with Tenable Identity Exposure right out of the box. We also have native apps available for QRadar, Splunk, and Phantom.
- Is Tenable Identity Exposure a cloud-based solution?
-
Our solution supports both cloud-based and on-prem deployments. There is no functional difference between these two deployment approaches.
- Can Tenable Identity Exposure scale to multi-org and multi-forest Active Directory deployments?
-
Some of the largest, most sensitive ADs are already protected by Tenable Identity Exposure. Our platform has been built as an enterprise-grade solution and its agent-less, AD-native architecture allows it to support complex, multi-org, multi-forest Active Directory deployments.
- How is Tenable Identity Exposure licensed?
-
Tenable Identity Exposure is licensed per enabled user account.
- Does Tenable Identity Exposure require privileged access to Active Directory to find weaknesses and respond to attacks?
-
Tenable Identity Exposure only requires a standard user account for auditing of configurations and the identification of attacks against Active Directory.
- How can I buy Tenable Identity Exposure?
-
You can purchase Tenable Identity Exposure by working with your local Tenable certified partner or contacting your Tenable representative.
- Is there an evaluation of Tenable Identity Exposure available?
-
Yes, evaluations are available of Tenable Identity Exposure, please fill out the evaluation request form to start your evaluation today.
Related resources
Get started with Tenable Identity Exposure
By deploying Tenable Identity Exposure on our global perimeter, we gave stakeholders much-needed visibility of corporate cybersecurity risks.
- Tenable Identity Exposure