CVE-2025-1097, CVE-2025-1098, CVE-2025-1974, CVE-2025-24513, CVE-2025-24514: Frequently Asked Questions About IngressNightmare
Frequently asked questions about five vulnerabilities in the Ingress NGINX Controller for Kubernetes, collectively known as IngressNightmare.
Update April 2: The blog has been updated to include the availability of a direct (remote) check plugin for CVE-2025-1974.
Background
The Tenable Security Response Team (SRT) has compiled this blog to answer Frequently Asked Questions (FAQ) regarding IngressNightmare.
FAQ
What is IngressNightmare?
IngressNightmare is the name given to a series of vulnerabilities in the Ingress NGINX Controller for Kubernetes, an open source controller used for managing network traffic in Kubernetes clusters using NGINX as a reverse proxy and load balancer.
What are the vulnerabilities associated with IngressNightmare?
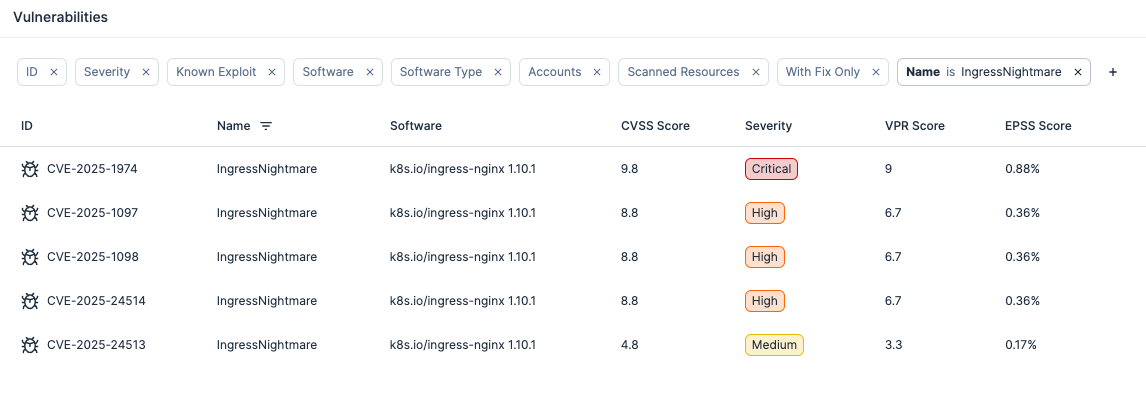
The following CVEs are associated with IngressNightmare:
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2025-1097 | Ingress NGINX Controller Configuration Injection via Unsanitized auth-tls-match-cn annotation | 8.8 |
| CVE-2025-1098 | Ingress NGINX Controller Configuration Injection via Unsanitized Mirror Annotations | 8.8 |
| CVE-2025-1974 | Ingress NGINX Admission Controller Remote Code Execution | 9.8 |
| CVE-2025-24513 | Ingress NGINX Controller Auth Secret File Path Traversal Vulnerability | 4.8 |
| CVE-2025-24514 | Ingress NGINX Controller Via Unsanitized Auth-URL Annotation | 8.8 |
When was IngressNightmare first disclosed?
Public disclosure of IngressNightmare happened on March 24 when news outlets, such as The Hacker News, began reporting on these vulnerabilities. At the time those articles were published, no patches were yet available from the Kubernetes team nor had a blog been published by the researchers who discovered these flaws.
How critical are the IngressNightmare vulnerabilities?
Based on the CVSS scores for these vulnerabilities, three are categorized as high severity, one is categorized as medium severity and one is categorized as critical severity.
The most severe flaw, CVE-2025-1974, requires an unauthenticated remote attacker to be able to access the admission controller, a component in the Ingress NGINX Controller that has more privileged access within a Kubernetes cluster.
Are the IngressNightmare vulnerabilities part of a toxic combination?
Yes, the five vulnerabilities that make up IngressNightmare can be chained together as part of a toxic combination (or exploit chain). Successful exploitation of these flaws would grant an attacker the ability to access cluster secrets, which could result in a cluster takeover.
Was this exploited as a zero-day?
No, these vulnerabilities were reported to Kubernetes through coordinated disclosure.
Is there a proof-of-concept (PoC) available for these vulnerabilities?
Yes, there are now multiple proof-of-concept (PoC) exploits [1, 2] published on GitHub that can exploit the IngressNightmare vulnerabilities to gain remote code execution.
Are patches or mitigations available for IngressNightmare?
Yes, on the evening of March 24, the Kubernetes team published two fixed versions of Ingress NGINX Controller:
| Affected product | Affected versions | Fixed version |
|---|---|---|
| Ingress NGINX Controller | 1.12.0 | 1.12.1 |
| Ingress NGINX Controller | 1.11.4 and below | 1.11.5 |
Additionally, customers can use the following command to determine if clusters are using ingress-nginx:
kubectl get pods --all-namespaces --selector app.kubernetes.io/name=ingress-nginxFor more specific information about mitigation steps, please refer to the Kubernetes blog.
Does this also affect the NGINX Ingress Controller?
No, while the names may sound similar, IngressNightmare does not affect the NGINX Ingress Controller from F5.
Has Tenable released any product coverage for these vulnerabilities?
A list of Tenable plugins for these vulnerabilities will be available on the individual CVE pages as they’re released:
Our Plugins Pipeline displays all available plugins for these vulnerabilities, including upcoming plugins, as they are added.
A direct (remote) check plugin, Kubernetes Ingress NGINX Controller Arbitrary Code Execution (CVE-2025-1974), is available.
Customers can also use our Kubernetes Ingress NGINX Controller Installed (Linux) plugin to identify assets with Ingress NGINX Controller installed.
Tenable Cloud Security can now scan for the IngressNightmare vulnerabilities across your cloud workloads and docker images detected in your cloud environments:
Additional coverage is being investigated by Tenable Research and this blog post will be updated accordingly.
Get more information
- Ingress-nginx CVE-2025-1974: What You Need to Know
- IngressNightmare: Vulnerabilities in Ingress NGINX
Change Log
Update April 2: The blog has been updated to include the availability of a direct (remote) check plugin for CVE-2025-1974.
Update March 27: The blog has been updated to include the availability of public proof-of-concept exploits for IngressNightmare as well as the latest Tenable product coverage, including Tenable Cloud Security coverage.
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Exposure Management
- Vulnerability Management
- Exposure Management
- Vulnerability Management


