Cybersecurity Snapshot: Guide Unpacks Event-Logging Best Practices, as FAA Proposes Stronger Cyber Rules for Airplanes

Looking to sharpen your team’s event logging and threat detection? A new guide offers plenty of best practices. Plus, the FAA wants airplanes to be more resilient to cyberattacks. Meanwhile, check out the critical vulnerabilities Tenable discovered in two Microsoft AI products. And get the latest on ransomware trends, vulnerability management practices and election security!
Dive into six things that are top of mind for the week ending August 23.
1 - Guide outlines logging and threat detection best practices
As attackers double down on the use of stealthy, hard-to-detect “living off the land” (LOTL) techniques, cybersecurity teams should improve how they log events and detect threats. That’s the call government agencies from multiple countries made in a joint guide published this week and titled “Best Practices for Event Logging and Threat Detection.”
“Event logging supports the continued delivery of operations and improves the security and resilience of critical systems by enabling network visibility,” reads the guide, which was developed by the Australian Cyber Security Centre (ACSC).

The guide, whose intended audience includes senior IT and operational technology (OT) leaders and operators, network administrators and critical infrastructure providers, groups its best practices under four categories:
- Enterprise-approved event logging policy, which includes event-log quality and the consistency of content, formats and timestamps
- Centralized log collection and correlation, which focuses on logging priorities for enterprise networks, OT systems, mobile devices and cloud environments
- Secure storage and event-log integrity, which touches on protecting logs from unauthorized access, modification and deletion
- Detection strategy for relevant threats, which deals with LOTL techniques, such as attackers’ use of legitimate tools and capabilities in the breached environment
The guide’s recommendations can help “detect malicious activity, behavioral anomalies, and compromised networks, devices, or accounts,” reads a statement from the U.S. Cybersecurity and Infrastructure Security Agency (CISA), which collaborated with the ACSC, along with cyber agencies from seven other countries.
To get more details, check out:
- CISA’s announcement
- The full 17-page guide “Best Practices for Event Logging and Threat Detection”
For more information about event logging and threat detection:
- “Security log management and logging best practices” (TechTarget)
- “Logging Cheat Sheet” (OWASP)
- “Network security logging and monitoring” (Canadian Centre for Cyber Security)
- “Introduction to logging for security purposes” (U.K. NCSC)
2 - FAA wants to tighten aviation cyber rules
To beef up the aviation sector’s cyber defenses, the U.S. government this week proposed new cybersecurity rules for airplanes, engines and propellers as they become increasingly connected to computer networks and services.
In a proposed rulemaking notice, the U.S. Federal Aviation Administration (FAA) said some of its regulations are “inadequate and inappropriate to address the cybersecurity vulnerabilities caused by increased interconnectivity.”
Current designs for airplanes can make them vulnerable to cyber risks from maintenance laptops; airport or airline networks; the internet; wireless sensors and their networks; USB devices; and cellular and satellite systems and communications; and more.

The proposed new and revised rules seek to protect airplanes, engines and propellers from “intentional unauthorized electronic interactions” (IUEI) so the FAA wants to require product designers and makers to “identify” and “assess” IUEI risks and mitigate them.
To that end, they would need to conduct a security risk analysis to identify all cyberthreats, assess threat severity, determine exploitation likelihood and mitigate these security issues.
The proposed rules are now open for public comment.
To get more details, check out the 36-page notice of proposed rulemaking titled “Equipment, Systems, and Network Information Security Protection.”
For more information about aviation cybersecurity:
- “TSA, FAA Requirements Emphasize Cybersecurity for Airport and Aircraft Operators and Airport Terminal Projects” (Tenable)
- “Aviation Cybersecurity: Risks and Mitigations” (National Business Aviation Association)
- “Why aviation needs to prioritise cybersecurity” (Airport World)
- “Protecting The Aviation Sector From Cyberattacks” (Tenable)
3 - Tenable finds critical vulnerabilities in two Microsoft AI products
Tenable Research recently discovered critical vulnerabilities in Microsoft’s Azure Health Bot Service and Copilot Studio.
In the case of Azure Health Bot Service, a cloud platform for deploying AI-powered virtual health assistants, the critical vulnerabilities allowed researchers access to cross-tenant resources within this service.
Meanwhile, a server-side request forgery (SSRF) vulnerability in Copilot Studio allowed researchers access to potentially sensitive information regarding service internals with potential cross-tenant impact. With Copilot Studio, you can build custom Copilot conversational applications for performing large language model (LLM) and generative AI tasks.
To get all the details, read these Tenable blogs:
- “SSRFing the Web with the Help of Copilot Studio”
- “Compromising Microsoft's AI Healthcare Chatbot Service”
You can also find media coverage of the two discoveries here:
Copilot Studio
- “Microsoft Copilot Studio Exploit Leaks Sensitive Cloud Data” (Dark Reading)
- “Microsoft Copilot Studio Vulnerability Led to Information Disclosure” (SecurityWeek)
- “Microsoft Patches Critical Copilot Studio Vulnerability Exposing Sensitive Data” (The Hacker News)
Azure Health Bot Service
- “Microsoft's AI Health Bot required patching for privilege vulnerability” (Healthcare IT News)
- “Fix for Azure Health Bot vulnerabilities prevents exploitation” (TechTarget)
- “Microsoft Azure AI Health Bot Infected With Critical Vulnerabilities” (Dark Reading)
4 - Tenable polls webinar attendees on vulnerability management practices
During our recent webinar “From Frustration to Efficiency: Optimize Your Vulnerability Management Workflows and Security with Tenable,” we polled attendees on their biggest vulnerability management challenge and on patching prioritization. Check out what they said!
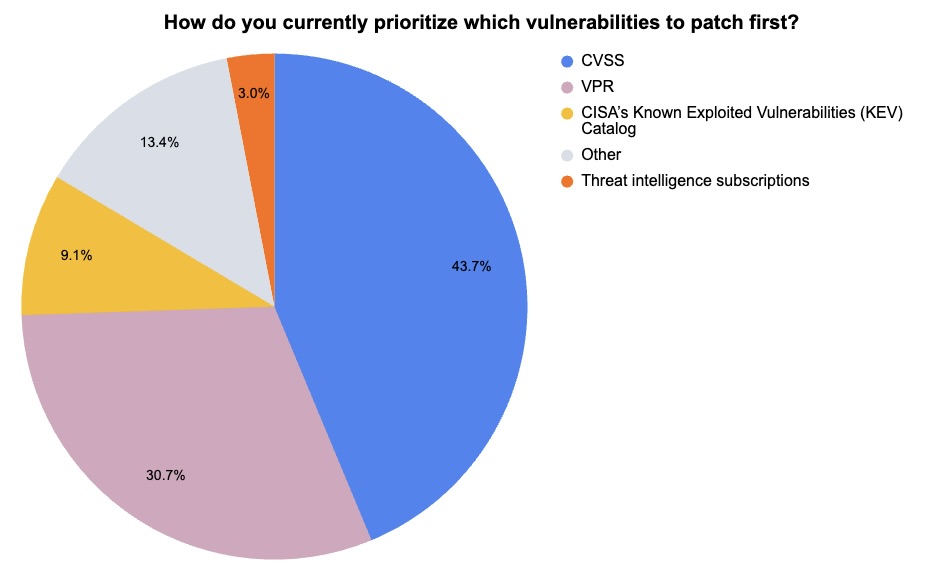
ƒ(231 webinar attendees polled by Tenable, August 2024)
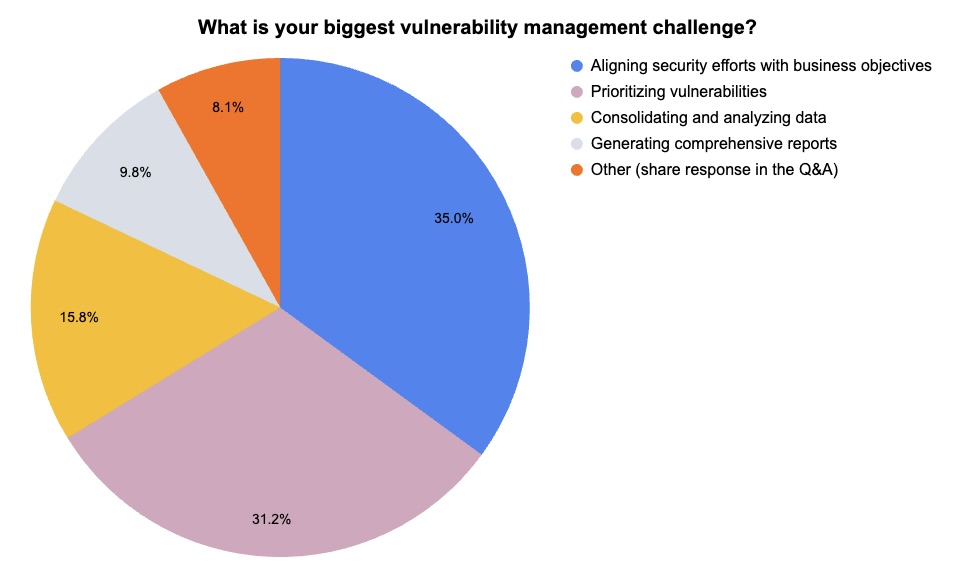
(234 webinar attendees polled by Tenable, August 2024)
Want to learn how to improve key vulnerability management practices, including remediation prioritization? Watch this on-demand webinar “From Frustration to Efficiency: Optimize Your Vulnerability Management Workflows and Security with Tenable.”
5 - Report: Ransomware attacks jumped in July, as attackers turn to infostealer malware
Ransomware attacks spiked 20% globally in July, compared with June, as the RansomHub gang emerged as the most active group.
However, ransomware attacks were down compared with July 2023, and “remain much lower” compared with the activity observed between February to May of this year.
That’s according to the “Monthly Threat Pulse” report for July 2024, published this week by NCC Group’s Global Threat Intelligence team.
“Whether this increase reflects the start of an upward trend remains to be seen,” the report reads.
Global Ransomware Attacks by Month 2023 - 2024
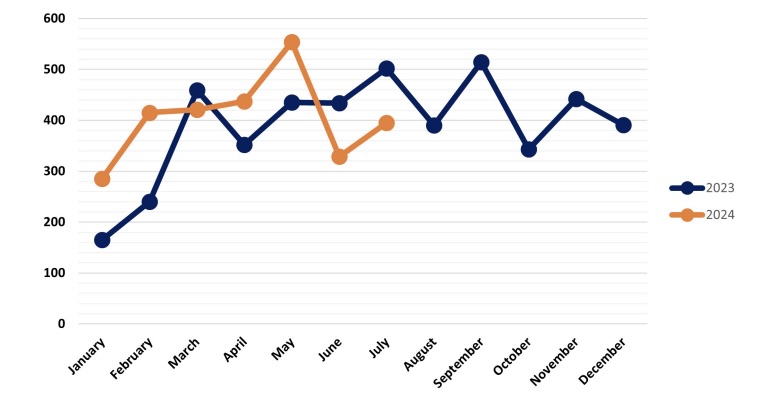
(Source: “Monthly Threat Pulse” report from NCC Group, August 2024)
The industrials sector was the hardest hit, receiving about a third of all attacks, a clear sign of ransomware groups’ strong interest in breaching critical-infrastructure organizations, the report says.
Ransomware groups pounced on CVE-2024-37085, an authentication-bypass vulnerability in the VMware ESXi hypervisor product, a reminder that organizations need to continue to prioritize patching high-risk bugs.
While vulnerability exploitation remains a popular tactic for ransomware attackers, they’re also increasing their use of information stealer malware, which offers them a “far easier, faster and often cheaper” way to access a network via the use of stolen credentials, the report reads.
“The rise in sophisticated techniques, such as the use of information stealer malware in their pre-attack phase, highlights that cybercriminals are not standing still. As these threats evolve, so must our defences,” Ian Usher, Deputy Head of Threat Intelligence at NCC Group, said in a statement.
To get more details, check out:
- The report’s announcement
- The “Monthly Threat Pulse Review of July 2024”
For more information about ransomware trends:
- “Ransomware Is ‘More Brutal’ Than Ever in 2024” (Wired)
- “Ransomware on track for record profits, even as fewer victims pay” (SC Magazine)
- “Ransom recovery costs reach $2.73 million” (Help Net Security)
- “Ransomware report finds 43% of data unrecoverable after attack” (SC Magazine)
6 - CISA: Ransomware won’t impact U.S. presidential election
Although ransomware gangs may try to disrupt the U.S. general election, their attacks won’t compromise the voting and counting processes, according to CISA and the FBI. At best, ransomware attacks would cause isolated delays and be minimally disruptive.
“The public should be aware that ransomware is extremely unlikely to affect the integrity of voting systems or the electoral process,” FBI Cyber Division Deputy Assistant Director Cynthia Kaiser said in a statement.
The reason: U.S. election officials have put in place what CISA and the FBI call a “multi-layer approach to security” with a variety of technical, physical and procedural safeguards.
“In the event of a ransomware event affecting their offices, election officials have plans and redundancies in place to allow voting operations to continue so that all eligible voters are able to cast their ballot securely,” reads a joint public-service announcement from CISA and the FBI.
To get more details, check out:
Learn more
- Cloud
- Cybersecurity Snapshot
- Event Monitoring
- Risk-based Vulnerability Management
- Threat hunting
- Threat Intelligence




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success