by Josef Weiss
January 19, 2022
Organizations must know the existence and location of critical assets to ensure that assets are monitored and protected based on each asset’s business risk rating. Identifying assets facilitates vulnerability scanning and remediation by ensuring that scans are configured to probe for common weaknesses in the platform or application. Discovering all assets enables organizations to establish an inventory, which can be used to assess and mitigate associated risks to the organization.
Attacker vectors are global. Attackers continuously scan the address space of target organizations, looking for new and unprotected systems to be attached to the network. Maintaining a comprehensive and up-to-date asset inventory is a fundamental and critical component of Risk-Based Vulnerability Management (RBVM). Asset identification of all connected assets within an organization is a common baseline requirement in a number of security standards, such as NIST Special Publication 800-53 and General Data Protection Regulation (GDPR). Maintaining an asset inventory is also the critical first step in the Discovery phase of RBVM, allowing organizations to be more proactive.
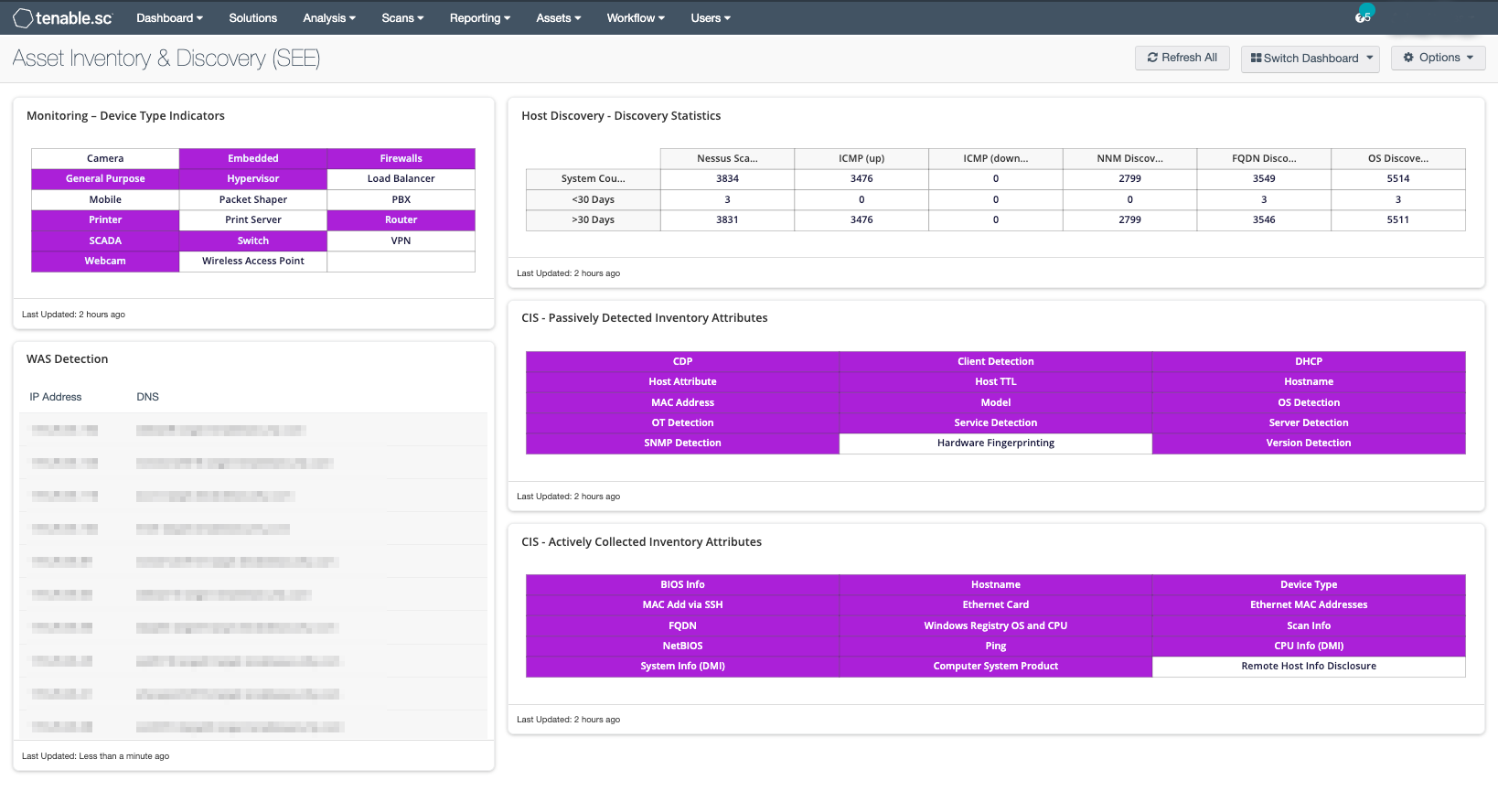
This dashboard provides guidance to establish an asset discovery, including:
- Actively and passively detected assets
- Asset discovery statistics
- Detected web applications
- Indications for device types (printers, cameras, routers, firewalls, WAPs)
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards (ARCs), and assets. The dashboard is located in the Tenable.sc Feed in the Discovery and Detection category.
The dashboard requirements are:
- Tenable.sc 5.20.0
- Nessus 10.0.2
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.sc discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture.
This dashboard contains the following components:
- Monitoring - Device Type Indicators - This component uses the Device Type plugin and displays all existing device types.
- WAS Detection - This component provides an updated list of Web Applications detected by Tenable.io WAS and displays the Last Seen date.
- SEE - Host Discovery - Discovery Statistics - This matrix provides a high-level view of host discovery, depicting the detection method, such as Nessus scanned, NNM discovered, or OS Discovered.
- CIS - Passively Detected Inventory Attributes - This component displays passively collected asset attributes that can be used to build an asset inventory.
- CIS - Actively Collected Inventory Attributes - This component displays actively collected asset attributes that can be used to build an asset inventory.