by Cody Dumont
Critical network systems are susceptible to misconfigurations which lead to a compromised network. CIS provides organizations with a series of configuration hardening benchmarks. This dashboard provides organizations with a compliance summary of network devices.
The CIS ControlsTM are a prioritized set of actions that collectively form a defense-in-depth set of best practices that mitigate the most common attacks against systems and networks. These controls were developed by IT professionals using operational experiences and generally accepted best practices; this dashboard will focus on Control 11 (Secure Configuration for Network Devices, such as Firewalls, Routers, and Switches).
Historically CIS has referred the first six CIS controls as cyber hygiene to focus an organization’s cybersecurity activities. The designation of cyber hygiene brought up the fact that these practices may be difficult for organizations with resource and/or expertise limitations. To address any resource or expertise limitation, CIS now recommends following Implementation Groups (IG) to help prioritize CIS control utilization. There are three IG’s, which describe organization by size. The IG specifies a subset of the controls that have been assessed to have a similar risk profile and resources to implement. The IG’s are also meant to be prioritized in IG order regardless of the IG organization size; for example, organizations should implement Sub-Controls in IG1, followed by IG2 and then IG3. The IG’s are described as organizations with limited resources and cybersecurity expertise (IG1); Organizations with moderate resources (IG2); Organizations with significant resources (IG3).
Installing the latest stable version of the operating systems or software is the only sub control required by all IG’s. The remaining 6 sub controls are required by IG2 and IG3. Tenable.sc provides innovative way to find vulnerabilities for network devices using different attributes, such as the Common Platform Enumeration (CPE). In this dashboard, there are components using the CPE find current vulnerabilities and trending.
The control requires organizations to establish, implement, and actively manage the security configuration of network infrastructure devices using a rigorous configuration management and change control process in order to prevent attackers from exploiting vulnerable services and settings. Fortunately, CIS also provides an extensive list of configuration benchmarks to facilitate the establishment of said security configurations. Furthermore, Tenable.sc is equipped with a series of audit files that can assess these devices against the CIS Benchmarks. While each benchmark has a corresponding report template, this dashboard provides a high-level summary of all audit configurations related to CIS benchmarks, and other components focused on general best practices. Tenable.sc uses a cross reference mechanism to correlate check from one standard to another. Tenable.sc is a complete solution for monitoring system hardening.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Executive.
The dashboard requirements are:
- Tenable.sc 5.12.0
- Nessus 8.8.0
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provide the ability to Analyze network assets for secure configurations and install the latest stable operating systems. Tenable.sc provides customers with a full and complete Cyber Exposure platform for completing an effective Cyber Hygiene program prescribed by CIS Controls framework.
This dashboard contains the following components:
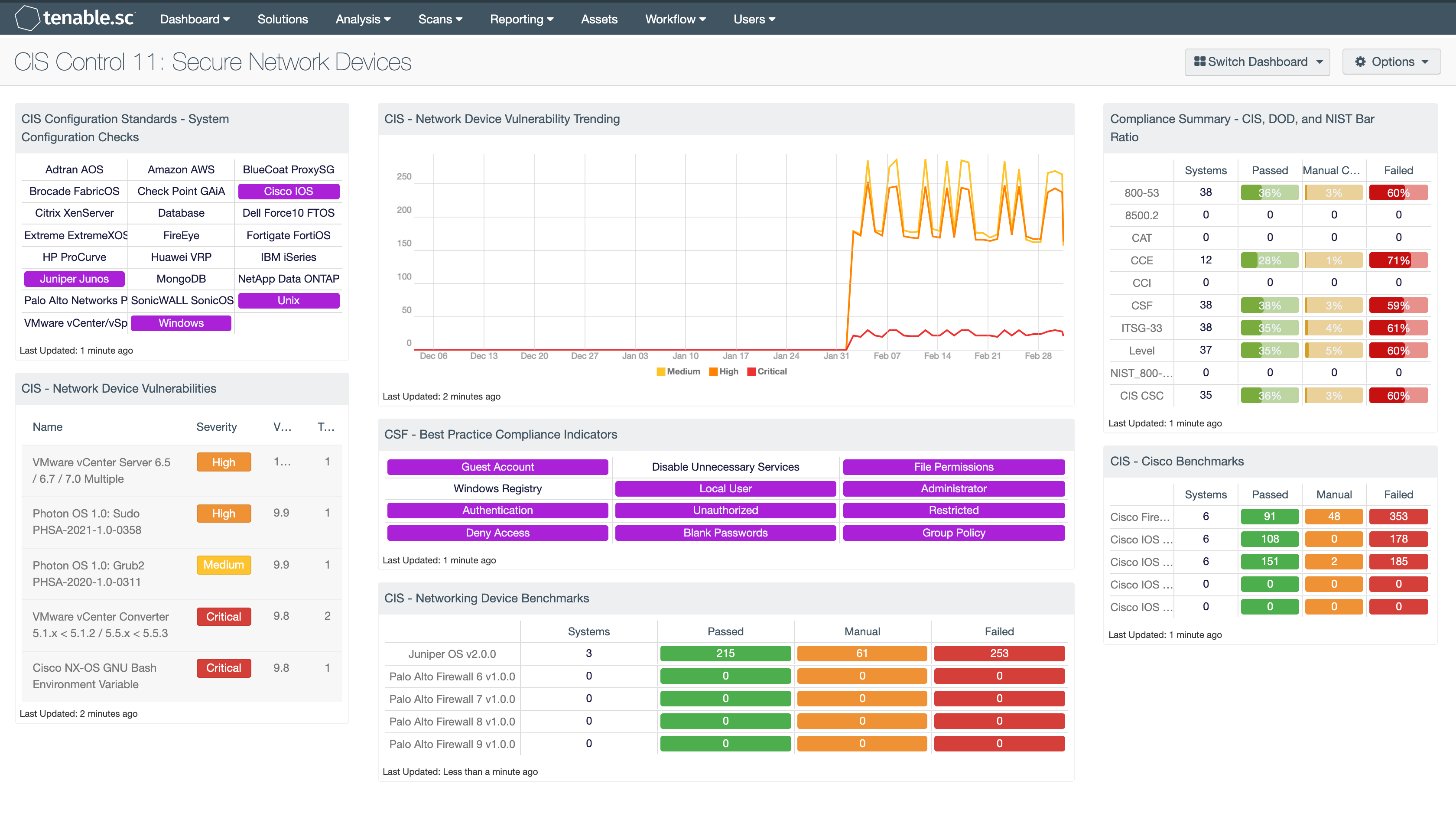
CIS - Network Device Vulnerabilities: Tenable.sc provides innovative ways to find vulnerabilities for network devices using different attributes, such as the Common Platform Enumeration (CPE). In this component, Tenable.sc uses CPE strings “bluecoat, brocade, check_point, checkpoint, cisco, citrix, dell, f5, fortinet, hp, huawei, juniper, netapp, netgear, paloaltonetworks, pfsense, sonicwall, ssh, veritas, vmware, websense” to locate vulnerabilities that are likely related to network devices. These vulnerabilities help to support CIS sub control 11.4 (Install the Latest Stable Version of Any Security Related Updates on All Network Devices).
CSF - Best Practice Compliance Indicators: This component uses results from the compliance audit to trigger on specific plugin keywords for best practice configuration guidelines. When the keyword or phrase has been detected within the plugin name, the indicator will turn purple. The analyst can click on the indicator and drill down to obtain additional information on hosts affected. This matrix will allow the analyst to readily identify specific compliance best practice keywords, and can be modified to suit organizational needs.
CIS - Network Device Vulnerability Trending: Tenable.sc provides innovative way to find vulnerabilities for network devices using different attributes, such as the Common Platform Enumeration (CPE). In this component, Tenable.sc uses CPE strings “bluecoat, brocade, check_point, checkpoint, cisco, citrix, dell, f5, fortinet, hp, huawei, juniper, netapp, netgear, paloaltonetworks, pfsense, sonicwall, ssh, veritas, vmware, websense” to locate vulnerabilities that are likely related to network devices. These vulnerabilities help support CIS sub control 11.4 (Install the Latest Stable Version of Any Security Related Updates on All Network Devices). The trend line is calculated over 3 months, and using the Last Observed Filter set to “Within the Last Day”. This allows analysts to track changes from one day to the next, showing a more accurate change. If scans are run weekly, then a user should modify the field to 7 days, so the change from scan to scan is accurately measured.
CIS - Networking Device Benchmarks: This matrix component presents a summary of audit checks performed on systems running Networking Device. The “Systems” column includes a count of the number of systems scanned against the audit check, and shows whether the operating system, service, or application is installed. Lack of results within the “Systems” column may highlight systems where the object in question is not installed, or the scan needs to be modified. The “Passed” column displays the number of scan results where the audit check passed the defined threshold within the CIS benchmark. The “Manual Check” column displays the number of scan results which require a manual review of the audit check to determine a pass or fail. The “Failed” column displays the number of scan results where the audit check was outside of the defined parameter in the CIS benchmark. These failed results should be addressed immediately.
Compliance Summary - CIS, DOD, and NIST Bar Ratio: This component displays a summary over of several audit standards, providing a host count, and ratio bars for each severity level. The compliance standards in this component are: NIST, DoD, CCE, CCI, CSF, and CSC. The three columns with ratio bars provide a ratio of total audit checks to a specified status of the check. Checks that have passed are green, failed are red, and checks which require manual verification are in orange.
CIS Configuration Standards - System Configuration Checks: This component provides indicators for CIS audits based on the device audited. The indicators search on two fields, the Cross Reference and vulnerability text. The Cross Reference uses the audit file keyword search, while the plugin text searches for “cisecurity.org”. These indicators will show the analysts which type of CIS audits have been run and provide an easy method for accessing CIS audit data. The indicators will turn purple when a match is discovered.
CIS - Cisco Benchmarks Benchmarks: This matrix component presents a summary of audit checks performed on systems running Cisco Benchmarks. The “Systems” column includes a count of the number of systems scanned against the audit check, and shows whether the operating system, service, or application is installed. Lack of results within the “Systems” column may highlight systems where the object in question is not installed, or the scan needs to be modified. The “Passed” column displays the number of scan results where the audit check passed the defined threshold within the CIS benchmark. The “Manual Check” column displays the number of scan results which require a manual review of the audit check to determine a pass or fail. The “Failed” column displays the number of scan results where the audit check was outside of the defined parameter in the CIS benchmark.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success