by Cody Dumont
September 30, 2015
Malware writers are continuing to evolve their processes and write code that is more difficult to track. However, malware leaves other traces within the network, which are called Indicators of Compromise (IOCs). Wikipedia defines an IOC within computer forensics as an artifact observed on a network or in an operating system that, with high confidence, indicates a computer intrusion. Common types of IOCs are virus activity, known malicious actors via IP address, MD5 hash signatures of malware, domain names used by bot-nets, and other command and control activities. Tenable.sc Continuous View (CV) uses different detection methods to identify IOCs on an organization's network. This report template helps organizations identify system that may have been compromised.
Continuous network monitoring provides several methods of detecting IOCs. As defined by NIST, continuous network monitoring is “maintaining ongoing awareness of information security, vulnerabilities, and threats to support organizational risk management decisions”. Tenable CEO Ron Gula published this paper on continuous network monitoring. Using Tenable.sc CV, analysts can use active and passive scanning along with deep log analysis to hunt for malware.
To get started with continuous network monitoring, first start by passively scanning the network using Tenable’s Nessus Network Monitor (NNM). NNM sensors should be placed in strategic locations across the network. Next, set up the Log Correlation Engine (LCE) to collect logs from servers, network equipment, firewalls, and workstations. Also, ensure that NNM is sending log data to the LCE. Next, configure LCE to collect NetFlow and/or use the Network Monitor Agent, which allows the LCE to analyze network traffic in real time. Finally, as the organization starts to identify assets on the network, active scanning can begin using Nessus. Active scanning should use network credentials, and administrators should make sure that the scanning policies check for Windows AutoRuns, Banner Detection, Process Enumeration, and Service Enumeration.
Organizations will find this report useful when reviewed on a daily basis. While the report provides a 15-day log history, these events should be monitored for indicators of malware migration. This report provides an executive summary showing the affected networks and counts of vulnerabilities and events. The remaining four chapters provide a targeted subnet summary and detailed list of raw logs and vulnerability details. The report in some cases can become very long; however, the report is organized in a manner that is easy to distribute and easily use for investigative purposes.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.6.0
- LCE 6.0.0
- NNM 5.9.0
Tenable.sc Continuous View (CV) provides continuous threat intelligence, which is more than just vulnerability management. Tenable.sc CV allows organizations to identify IOCs, malware, malicious activity, trust relationships, suspicious events, and much more. Tenable.sc CV supports more technologies than any other vendor, including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Tenable covers all types of users and services, regardless of location, 100% of the time.
Chapters
Executive Summary: This chapter provides the executive team with a high level overview of subnets that have IOCs, which should be investigated. There are four sections, each dedicated to different type of IOCs. Each section contains a summary matrix and bar charts displaying the targeted information.
Indicators of Malware from Vulnerability Data: This chapter provides a summary of vulnerability data collected using credentialed scans and passive vulnerability detection. The primary focus of this content is rogue processes, botnet activity, and known backdoors.
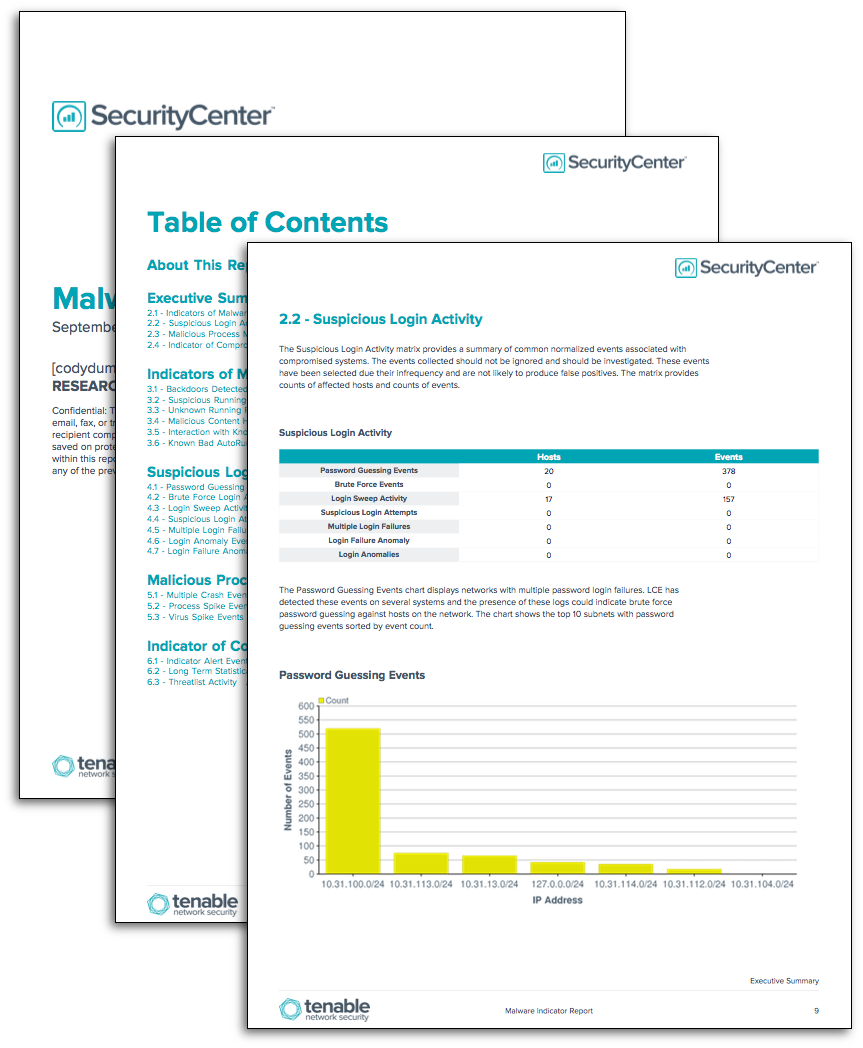
Suspicious Login Activity: This chapter provides a summary of common normalized events associated with compromised systems. The events collected should not be ignored and should be investigated. These events have been selected due their infrequency and are not likely to produce false positives.
Malicious Process Monitoring: This chapter contains details the on events related to malicious processes. The data is collected from LCE Clients or by collected syslog messages. The primary focus of this content is malicious processes.
Indicator of Compromise (IOC) Events: This chapter contains events related to IOCs. The data collected requires LCE Clients or syslog configuration. The primary focus of this content is correlated events that provide some indication of compromise. Each of these events is triggered from several events together, not a single event. These events should always be investigated to determine if the event is normal activity.