Synopsis
While researching Oracle WebLogic Docker containers, Tenable discovered a couple of mechanisms to recover the administrative password.
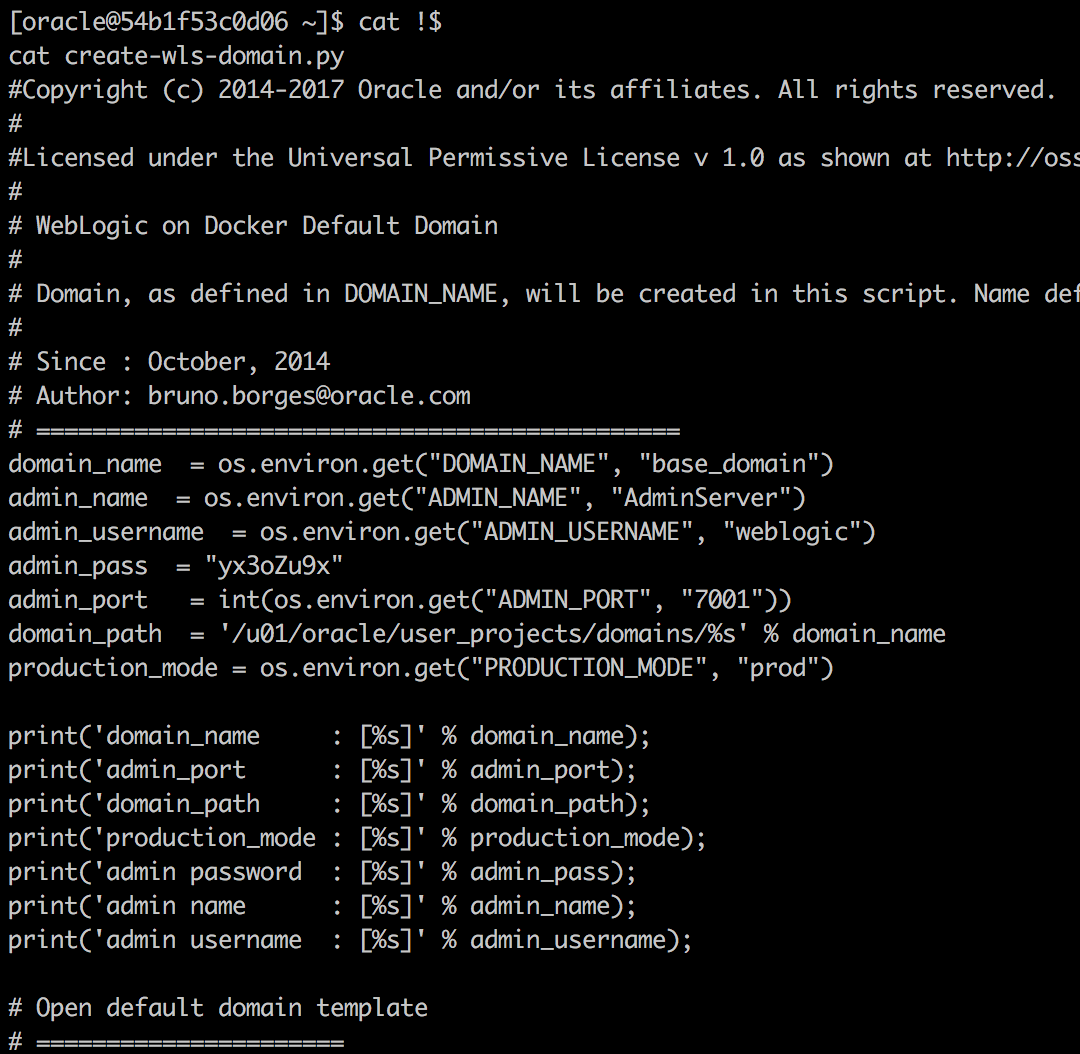
First, the container stores, in cleartext, the administrator's password in a script within the running container. That means anyone with access to the container can uncover the administrative password simply by executing cat create-wls-domain.py and locating the line that starts with admin_pass = . The following screenshot is an example:
Second, the administrator's password also finds its way into the container log. Anyone with access to the logs can simply run the following command to extract the password: docker logs [container id] | grep password.
Tenable notes that Oracle assigned a CVSSv3 score of 7.5 with a vector of AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N. However, this score seems off to us. Specifically, local access to the target is required. It's possible that Oracle found an additional and more severe vector, but they didn't inform Tenable as to what that vector is.
Solution
Oracle released fixes for these vulnerabilities on Github and as part of the October 2018 CPU. Follow Oracle's patching guidelines.Additional References
https://www.oracle.com/technetwork/security-advisory/cpuoct2018-4428296.htmlhttps://github.com/oracle/docker-images/pull/917
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success