Synopsis
Default password on Quagga Service (CVE-2021-20132)
CVSSv3 Vector: AV:A/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H (Base Score 8.8)
Arbitrary file read and denial of service (CVE-2021-20133)
CVSSv3 Vector: AV:A/AC:L/PR:H/UI:N/S:U/C:H/I:N/A:H (Base Score 6.1)
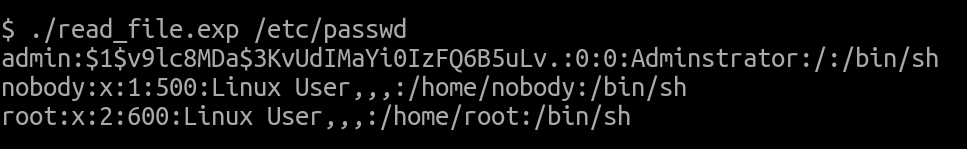
This will set the "message of the day" banner to contents of /etc/passwd. By logging back in, the attacker can retrieve the contents of the file. Long filess may be displayed only in part, and binary data will likely be corrupted, but reasonably short text files in the ASCII encoding can be read in their entirety in this fashion.
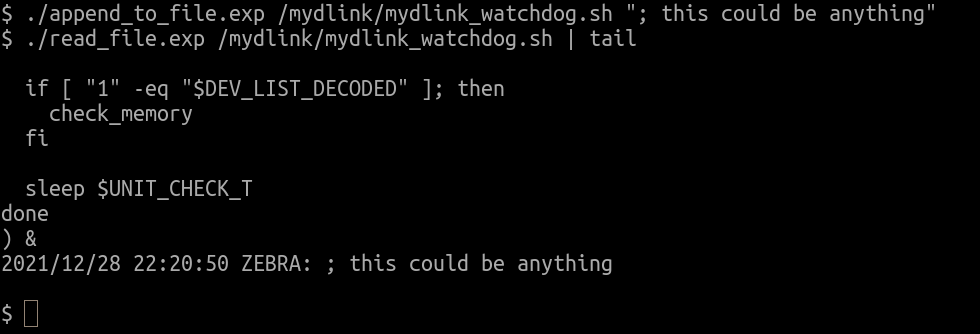
Arbitrary file append (CVE-2021-20134)
CVSSv3 Vector: AV:A/AC:L/PR:H/UI:N/S:C/C:H/I:H/A:H (Base Score 8.4)
Solution
This vulnerability remains unpatched at the time of writing. An intrepid user could, at their own risk, craft a shell command to disable the Quagga zebra and ripd services and then use the file-append vulnerability to write that command to the end of script that they know will be executed whenever the device is rebooted. In order for this to work, the target script would have to reside on one of the device's persistent filesystems, or the modifications would not survive a reboot. It is also possible to use the denial of service vulnerability described in the Synopsis to temporalily block access to either service.
Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success