by Cody Dumont
November 2, 2022
Scanning the network to detect vulnerabilities, open ports, and protocols is common practice. Internal scans are used to identify assets at risk and provide insight into the patch management process. Microsoft Active Directory servers – a key component of many networks – contain data about users, computers, applications, and shared resources, among other information. This dashboard uses output derived from a set of plugins that are part of the Tenable Active Directory Starter Scan Template to help organizations determine the security posture of their Active Directory Servers.
While many large data breaches reported in the media are conducted by external attackers, insider attacks continue to remain a significant source of data theft. The increasing complexity of organizational networks and the growing interconnection of many IT dimensions, including OT, cloud, and web applications, has opened new opportunities for adversaries. Active Directory (AD) is a favorite target for attackers to elevate privileges and facilitate lateral movement through a network. If an external attack is successful in providing access to the internal network, poorly configured AD servers can provide additional attack vectors.
Organizations face challenges inside the network managing employees, contractors, consultants, guests, and other authorized users, all with varying levels of access. Insiders have advanced knowledge of organizational security practices, and know where data is stored. AD Vulnerabilities can potentially allow local attackers to escalate permissions and gain access to assets that would otherwise be restricted.
Active Directory attacks typically fall under 2 categories:
- Passwords and credentials protection
- Privilege escalation & lateral movement prevention
The Active Directory Starter Scan Template contains 10 hygiene checks that are often exploited by attackers seeking to navigate their targets' Active Directory. These plugins focus on the most common attack paths, such as guessing or cracking accounts’ secrets, impersonating other users, privilege escalation and lateral across domains.
Specifically, these components assist organizations in the identification of potentially hard to spot attacks such as Golden Ticket attacks. Outside of legacy protocols, weak passwords, and accounts with elevated privileges, Golden Ticket Attacks are the most common attack against AD servers. Golden Ticket attacks center around Kerberos and KRBTGT (Kerberous Ticket Granting Ticket) - such as Kerberoasting - which are easy to successfully launch from the internal network. Kerberoasting is an attack that enables privilege exploitation, furthering the ability of an attacker to move laterally in the network.
These attacks are dangerous since the attacker does not require administrative rights. An attacker can simply request a service ticket from the Domain Controller and then use password cracking tools offline to retrieve plaintext credentials from vulnerable hashes. Active Directory vulnerabilities that can benefit attackers are also identified, such as Null Sessions, Primary Group ID, Weak Encryption, and Dangerous Trust Relationships.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.io discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture. The requirements for this dashboard are: Tenable.io Vulnerability Management (Nessus).
Widgets
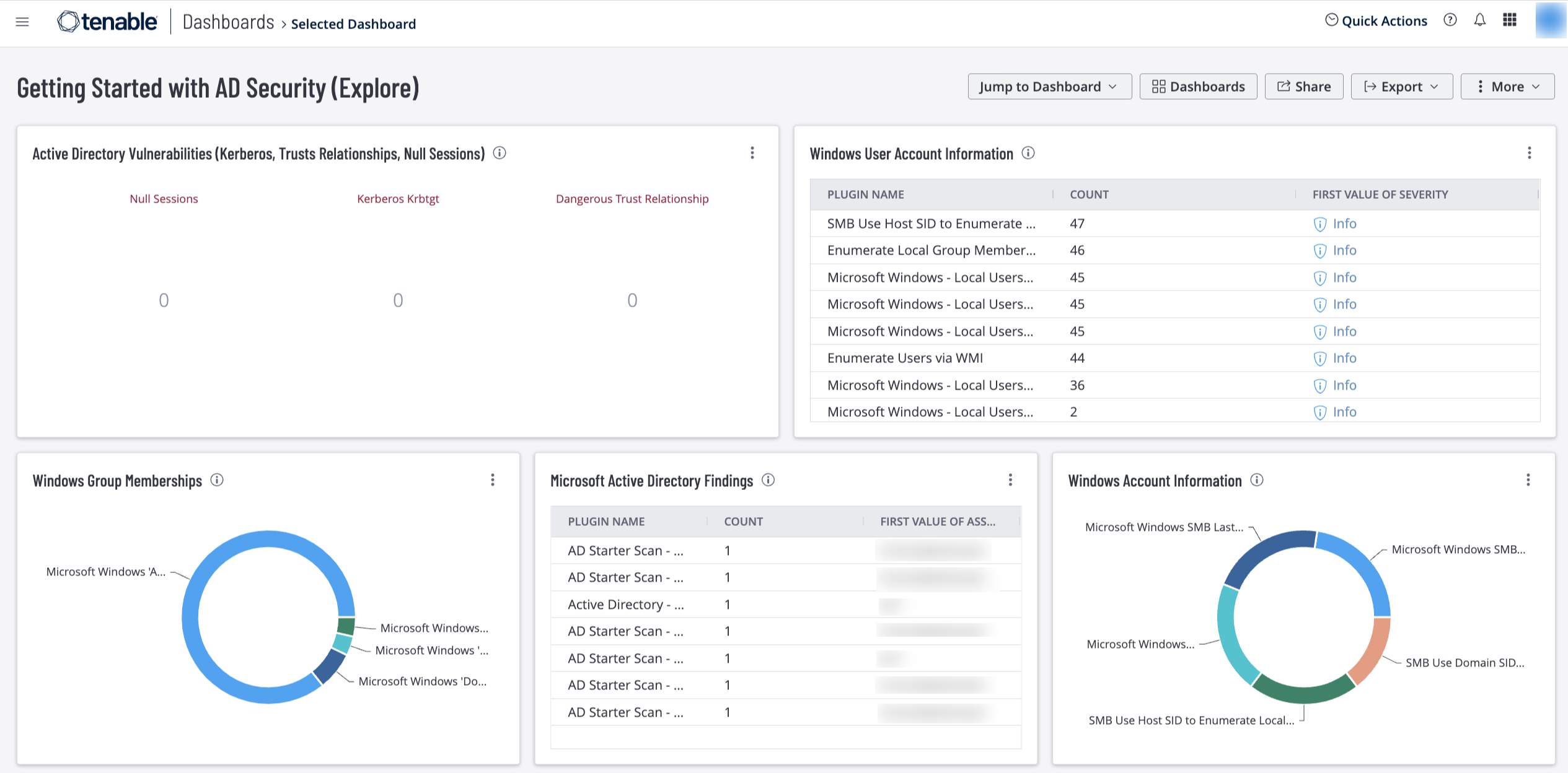
Active Directory Vulnerabilities (Kerberos, Trusts Relationships, Null Sessions) – This widget widget uses plugins 150488, 150484, and 150486 to list a total count of findings for assets that were identified with the Active Directory vulnerabilities plugins directly related to Kerberos, Trusts Relationships, and Null Sessions. These vulnerabilities represent misconfigurations that could lead to exploitation. The plugins used in this widget are part of the Active Directory Starter Scan template and are intended to be used for preliminary analysis of AD hosts. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Windows User Account Information – This widget displays counts for user accounts and security identifiers (SID). Plugins report on potential user account vulnerabilities such as disabled accounts, accounts that have never logged in, accounts with passwords that have never changed, and more. The widgets provide detailed information to determine if user accounts have any concerns that warrant further investigation. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Windows Group Memberships – This widget displays information for Windows default groups such as administrators, server operators, account operators, backup operators, print operators, and replicator groups. This information enables analysts to determine if appropriate role-based access controls are in place. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).
Microsoft Active Directory Findings – This widget displays a vulnerability summary for assets that contain any vulnerabilities related to Active Directory. This widget uses the application CPE filter to cross reference Tenable plugins that contain active_directory, including those from the AD Starter Scan. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus, NNM).
Windows Account Information – This widget displays counts related to Microsoft Windows SMB plugins that focus on user account information. Plugins focus on vulnerabilities such as SMB blank administrator passwords, SMB password policies, guest accounts, cached passwords, and more. The widget provides detailed information of Windows SMB accounts to determine if user accounts have any concerns that warrant further investigation. The requirements for this widget are: Tenable.io Vulnerability Management (Nessus).