by Carole Fennelly
May 24, 2022
New digital platforms and development shifts have rapidly moved from concept to capability. Tracking updates for the constantly changing landscape of assets is important to identify legacy code and asset footprint. This report focuses on legacy patches and assets to reduce management effort and reactive firefighting. Organizations can also identify parts of their network that have been missed by patching cycles, or where traditional mitigation methods no longer apply.
The rapid expansion of assets increases the importance to maintain continuous visibility to identify outdated technology and unpatched vulnerabilities. This report provides a clear snapshot of which assets are unsupported or unpatched.
As assets age, the process that secures them needs to evolve to stay ahead of legacy threats. Unpatched assets expose organizations to vulnerabilities that are actively being exploited. End of life assets may pose the greatest risk since they are unsupported and no longer receiving security updates or support from the vendor.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives.
Chapters
Outstanding Remediations - Time since Patch Publication: This matrix reflects three key points of risk: total count of missing patches, vulnerability severity, and exploitability ratio. Assets with the largest number of missing patches represent a higher level of mitigation effort and may be the most time consuming to address. Assets with a high exploitability ratio represent a fast lane for attackers. Mitigating these vulnerabilities is one of the best ways to reduce risk.
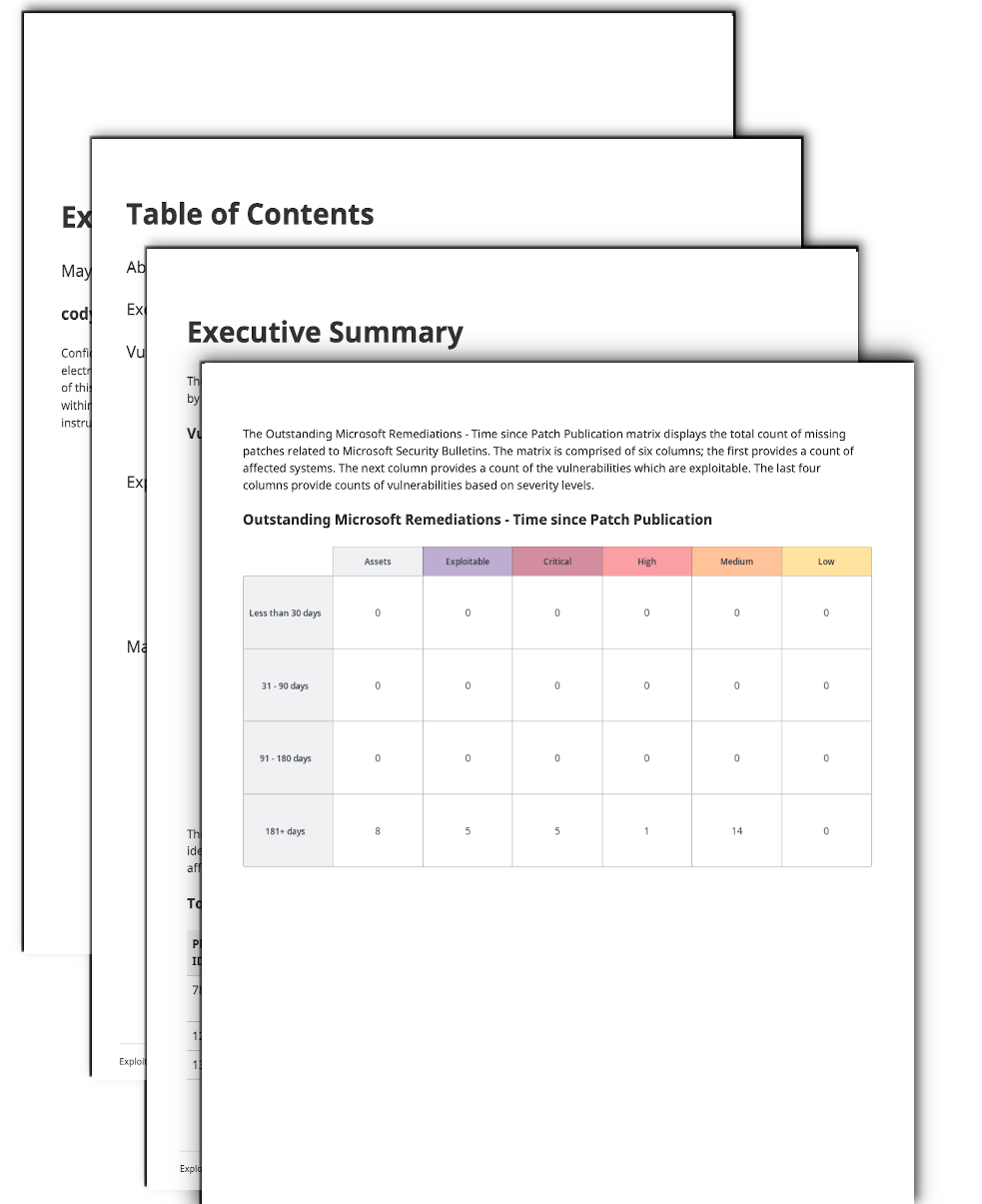
Outstanding Microsoft Remediations: Time since Patch Publication: This matrix reflects three key points of risk for Microsoft systems: total count of missing patches, vulnerability severity, and exploitability ratio. Assets with the largest number of missing patches represent a higher level of mitigation effort, and may be the most time consuming to address. Assets with a high exploitability ratio represent a fast lane for attackers. Mitigating these vulnerabilities is an effective way to reduce risk.
Outstanding Remediations by Device Type: This matrix reflects three key points of risk across different asset types: total count of missing patches, vulnerability severity, and exploitability ratio. Assets with the largest number of missing patches possibly represent a higher level of mitigation effort, and may be the most time consuming to address. Assets with a high exploitability ratio represent a fast lane for attackers. Mitigating these vulnerabilities is an effective way to reduce risk.
End of Life Software Detection: This table provides a look at which assets have reached their end of life from the vendor. All assets in this list have vulnerabilities that cannot be fixed by the vendor and can only be mitigated through upgrade or removal. Tenable recommends that assets found here be upgraded to a higher supported version as soon as possible, since vendors no longer list active vulnerabilities for end-of-life software.