by Cesar Navas
December 7, 2016
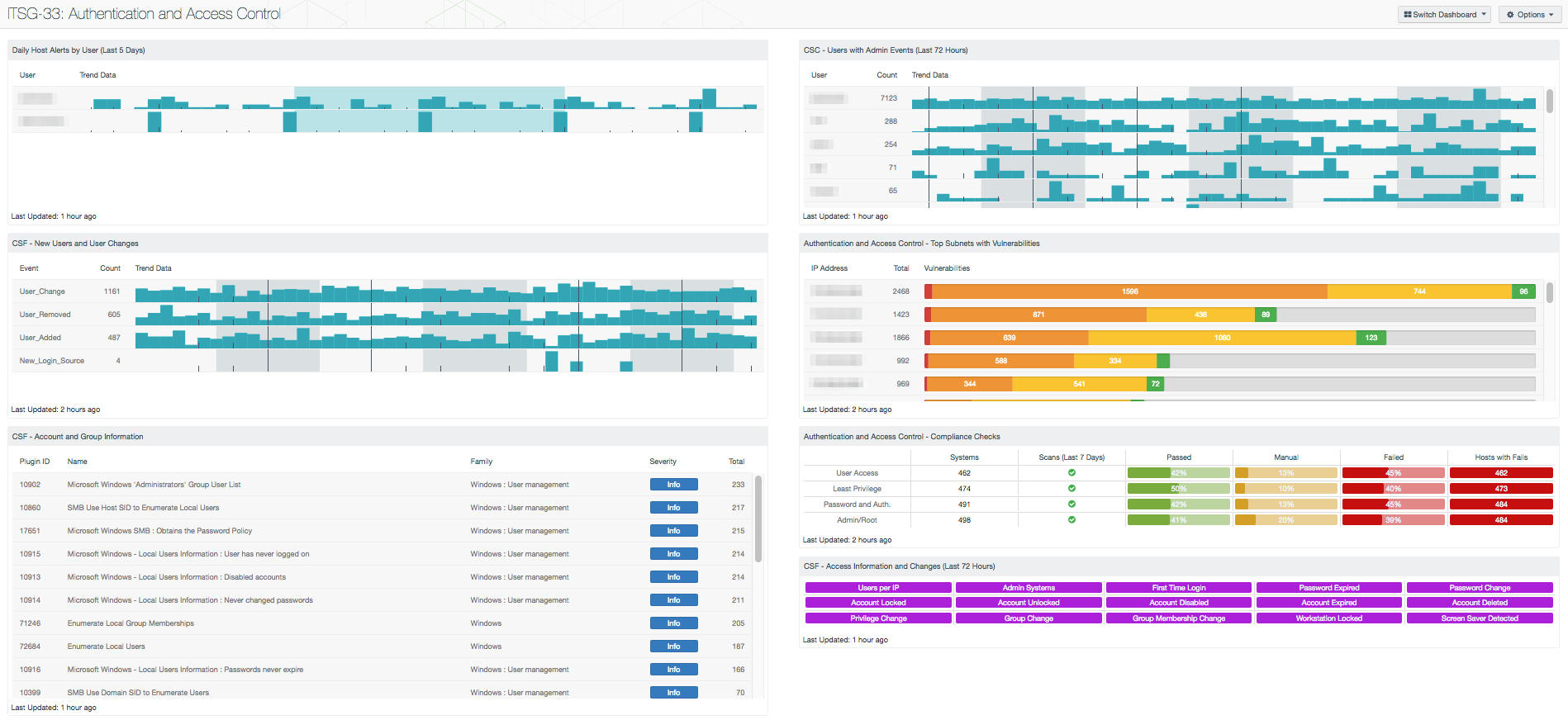
Organizations typically have a methodology of standardizing user accounts throughout the enterprise with products such as Microsoft Active Directory (AD). Using AD, a common structure for groups, permissions, and user accounts will quickly be standardized and kept consistent. When systems like AD are used, implementing certain regulatory guidelines from standards such as Canada’s Information Technology Security Guidance Publication 33 (ITSG-33) will be a straightforward task. The ITSG-33 guidance specifies standard configurations for critical areas of an organization, such as authentication and access control mechanisms.
The Communications Security Establishment Canada (CSEC) developed a series of guidelines for security practitioners in managing information technology (IT) security risks for Government of Canada (GC) information systems. The ITSG-33, IT Security Risk Management: A Lifecycle Approach provides a comprehensive set of security controls that will be used to support a wide variety of business requirements. To support interoperability needs, the ITSG-33 guide is consistent with controls published in the U.S. National Institute of Standards and Technology (NIST) Special Publication 800-53. Data presented within this dashboard aligns with ITSG-33 security controls that support the authentication mechanisms of information systems, and the access control methods used within those systems. This dashboard aligns with the following controls:
- Access Enforcement (AC-3)
- Account Management (AC-2)
- Identification And Authentication (IA-Family)
- Least Privilege (AC-6)
- Separation Of Duties (AC-5)
- Session Lock (AC-11)
- Session Termination (AC-12)
- System Use Notification (AC-8)
- Unsuccessful Logon Attempts (AC-7)
The information collected from active scanning, passive listening, and event monitoring will have a multitude of normal and expected activity that could quickly flood the analyst with noise. The components in this dashboard provide the analyst with relevant views into the data that is necessary to be reviewed. Important data that analysts should be concerned with include administrative events that should not change frequently, such as users being added to local administrative groups. Additionally, an administrative user account logging into multiple systems quickly across the organization should be investigated to validate appropriate activity. While many of these scenarios should be results from authorized and coordinated change control boards, unexpected activity will also be quickly identified. Continually reviewing this dashboard will keep analysts up to date on the important events relating to users and permissions, which could catch malicious activity.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.1
- Nessus 8.5.1
- NNM 5.9.0
- LCE 6.0.0
- complianceData
Tenables's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and assists in securing an organization’s internal network. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products is analyzed to monitor the network for malware, intrusions, and other forms of malicious activity. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to protect authentication and access control methods within the network.
The components in this dashboard include:
- Daily Host Alerts by User (Last 5 Days): This component shows when users generate alerts with hosts in the organization
- CSF - New Users and User Changes: This component presents data on new and existing user events on the network over the past 72 hours
- CSF - Account and Group Information: This table displays detections of account and group information, such as accounts that have never been logged into, disabled accounts, and group user lists
- CSC - Users with Admin Events (Last 72 Hours): This table presents those users associated with events that indicate performed or attempted administrative actions
- Authentication and Access Control - Top Subnets with Vulnerabilities: This component displays the top Class C subnets with actively and passively detected vulnerabilities related to authentication and access control
- Authentication and Access Control - Compliance Checks: This component displays compliance information in the areas of user access, least privilege, password and authentication requirements, and administrative/root account control
- CSF - Access Information and Changes (Last 72 Hours): This matrix component can help an analyst quickly pull up information on systems where certain user access-related events and changes have occurred