by Cody Dumont
October 7, 2016
The task of safeguarding a network in today's world is a formidable one. Mobile devices plus an increasing dependence on the internet and the cloud make maintaining control of network systems and data a nearly impossible job. The continuing discovery of product vulnerabilities and the advent of malware toolkits ensure that networks are bombarded by increasingly sophisticated attacks. Poor asset management, misconfigurations, inadequate user access controls, and insufficient network monitoring increase the risk that critical systems and data will be compromised. These issues can potentially lead to devastating consequences and even jeopardize an organization's competitiveness and long-term survival.
The French Network and Information Security Agency (Agence nationale de sécurité des systèmes d’information or ANSSI) developed the "40 Essential Measures for a Healthy Network" to assist organizations in safeguarding the security of information systems within a network. Following these measures, or rules, for a healthy network will provide basic protection for an organization's critical data. ANSSI states that the majority of IT attacks that have involved ANSSI stepping in could have been prevented had the IT measures set out in the guide been applied.
This report aligns with the ANSSI 40 Essential Measures for a Healthy Network and provides information to assist in achieving and maintaining compliance with the rules. The report covers the following sections:
- Section I: Know the Information System and Its Users
- Section II: Control the Network
- Section III: Upgrade Software
- Section IV: Authenticate the User
- Section V: Secure Computer Terminals
- Section VI: Secure the Inside of the Network
- Section VII: Protect the Internal Network from the Internet
- Section VIII: Monitor Systems
- Section IX: Secure Network Administration
- Section XI: Organise Response in the Event of an Incident
Using this report, organizations can obtain comprehensive information about inventory and can better monitor vulnerability patching and configuration compliance, both overall and in specific areas. Data on mobile devices and removable media that have connected to the network is presented, as well as wireless and remote access activity. User information, such as users performing administrative actions and users talking externally, can assist in understanding and controlling user access. Information on suspicious activity, such as suspicious logins, intrusion activity, hosts communicating with known bad IP addresses, and hosts infected with malware assists in identifying potential network compromises. An organization can use the information presented in this report to better secure and monitor the network. These improvements will enable better defenses against attacks and responses to malicious activity, and ultimately safeguard the organization's critical assets, data, and overall reputation.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- NNM 8.9.1
- LCE 6.0.0
- Tenable Network Monitor
- Tenable NetFlow Monitor
- Compliance data
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in knowing, managing, and securing the network. Active scanning periodically examines devices to determine vulnerabilities and compliance concerns. Agent scanning enables detection and scanning of transient devices. Passive listening collects data to continuously detect devices and monitor network connections and activity. Host data and data from other security investments is collected and analyzed to monitor activity, identify new assets, and detect anomalies and malicious behavior. Tenable.sc CV provides an organization with the most comprehensive view of the network, and the intelligence needed to safeguard critical assets and information.
Chapters
Executive Summary - This chapter gives a brief overview of the inventory, vulnerability, compliance, and user activity information presented in the rest of the report.
ANSSI I: Know the Information System and Its Users - This chapter aligns with Section I of the ANSSI 40 Essential Measures for a Healthy Network: Know the Information System and Its Users. From this chapter, an organization will obtain comprehensive information about assets, software installations, privileged user groups, and changes on the network.
ANSSI II: Control the Network - This chapter aligns with Section II of the ANSSI 40 Essential Measures for a Healthy Network: Control the Network. The information in this chapter will help an organization better monitor network connectivity, access control, and connections of mobile and removable devices.
ANSSI III: Upgrade Software - This chapter aligns with Section III of the ANSSI 40 Essential Measures for a Healthy Network guide: Upgrade Software. The information in this chapter will assist an organization in more effectively patching and updating the software on network systems.
ANSSI IV: Authenticate the User - This chapter aligns with Section IV of the ANSSI 40 Essential Measures for a Healthy Network: Authenticate the User. From this chapter, an organization will be able to obtain information about user accounts and groups, account and password vulnerabilities, and authentication compliance issues.
ANSSI V: Secure Computer Terminals - This chapter aligns with Section V of the ANSSI 40 Essential Measures for a Healthy Network: Secure Computer Terminals. From this chapter, an organization will be able to obtain information about configuration compliance failures and other policy-related concerns such as remote access and the use of portable devices and removable media.
ANSSI VI: Secure the Inside of the Network - This chapter aligns with Section VI of the ANSSI 40 Essential Measures for a Healthy Network guide: Secure the Inside of the Network. The information in this chapter will alert the organization to internal network product and protocol vulnerabilities, access control and least privilege issues, and wireless network concerns.
ANSSI VII: Protect the Internal Network from the Internet - This chapter aligns with Section VII of the ANSSI 40 Essential Measures for a Healthy Network: Protect the Internal Network from the Internet. The information in this chapter enables an organization to better understand how the internal network can be accessed externally and what security concerns are present.
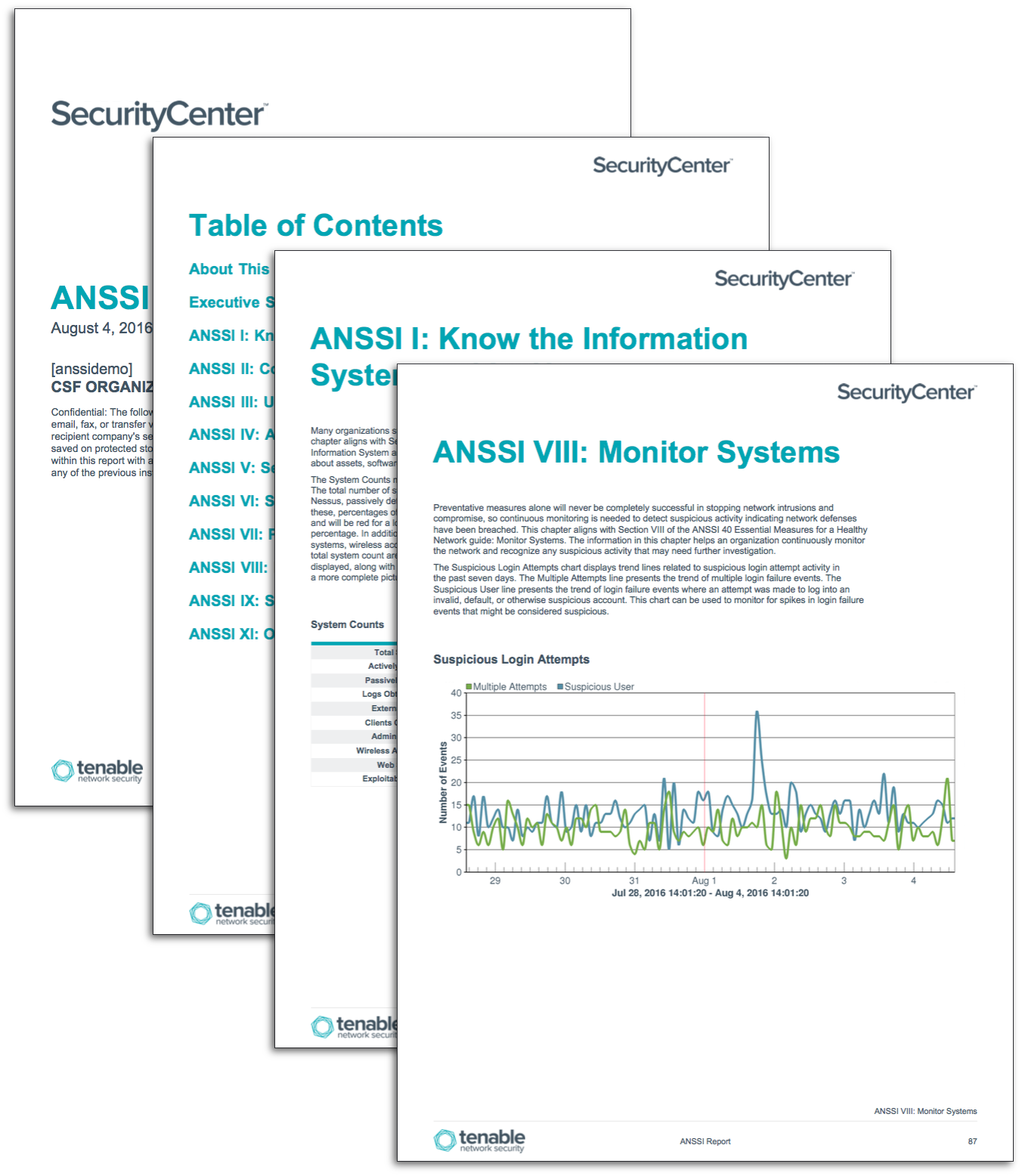
ANSSI VIII: Monitor Systems - This chapter aligns with Section VIII of the ANSSI 40 Essential Measures for a Healthy Network guide: Monitor Systems. The information in this chapter helps an organization continuously monitor the network and recognize any suspicious activity that may need further investigation.
ANSSI IX: Secure Network Administration - This chapter aligns with Section IX of the ANSSI 40 Essential Measures for a Healthy Network guide: Secure Network Administration. Information presented within this chapter will assist the organization in securing both administrative and remote access, which can help to ensure the overall security of the network.
ANSSI XI: Organise Response in the Event of an Incident - This chapter aligns with Section XI of the ANSSI 40 Essential Measures for a Healthy Network guide: Organise Response in the Event of an Incident. Organizations will be able to use the information presented in this chapter to understand current weaknesses and how to fix them, detect compromised hosts, and track incident response activity.