by Cody Dumont
March 16, 2017
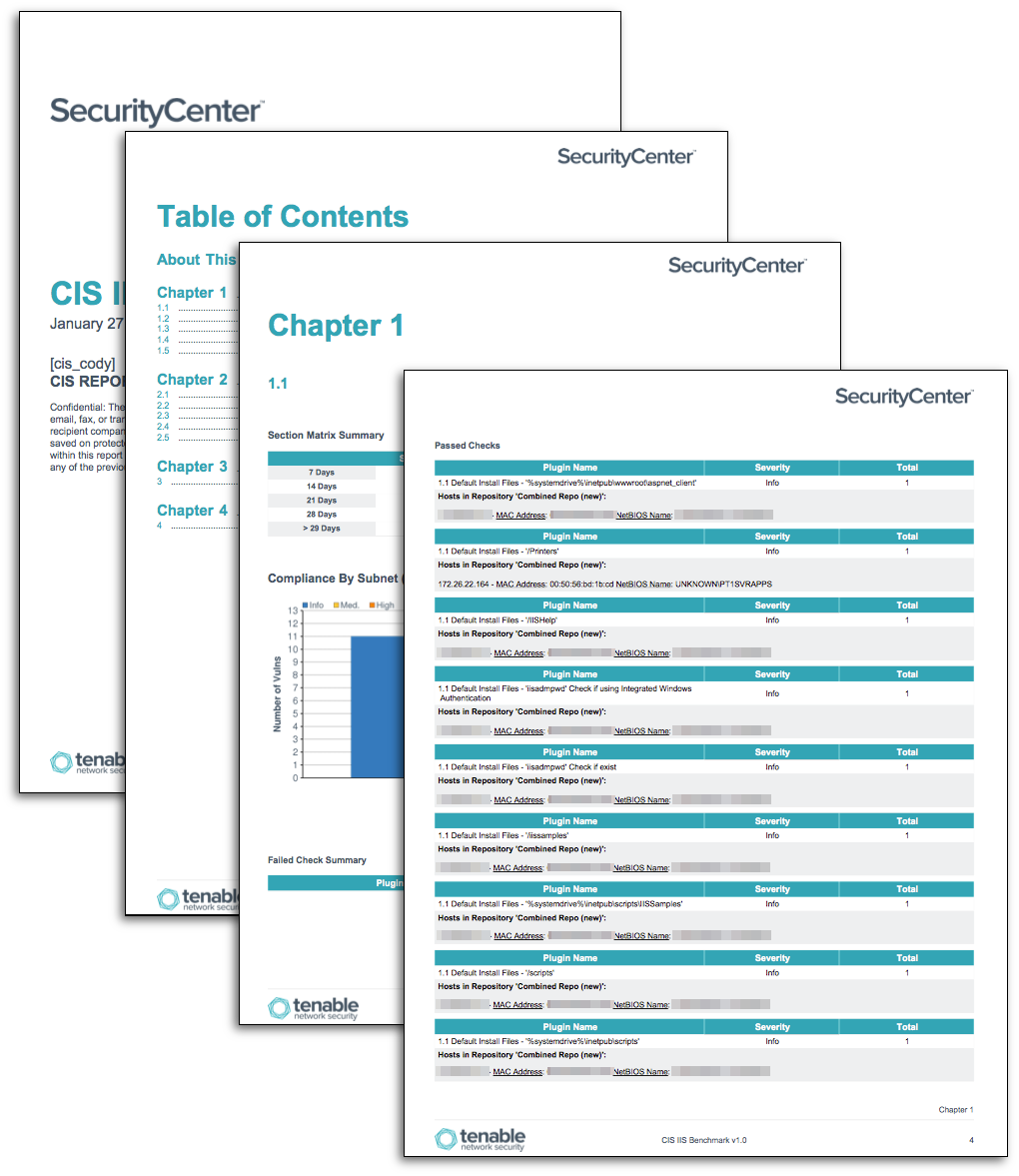
As web servers provide the primary interface between an organization and its customers, managing and securing these servers is a critical part of an organization’s overall security strategy. Even the most well managed and maintained web servers are still subject to vulnerabilities and attacks. Web servers are exposed directly to Internet and therefore are subject to continuous probing from malicious users. To effectively combat these attacks, organizations need to ensure web systems are hardened appropriately. The Center for Internet Security (CIS) is an organization that works with security experts to develop a set of 'best practice' security standards designed to harden operating systems and applications. The CIS created a series of hardening benchmarks guidelines for Microsoft Internet Information Server (IIS) web servers. These report templates provide a high-level overview of results gathered from CIS compliance scans using the CIS IIS Benchmarks.
Tenable Network Security has been certified by CIS to perform a wide variety of platform and application audits based on the best practice consensus benchmarks developed by CIS. Tenable submits example test cases for all of the criteria within each unique benchmark, and then submits our results to CIS personnel for official certification. Tenable developed audit files to support the CIS IIS Benchmarks tested on Microsoft Windows servers, and has been approved and certified by CIS staff members.
When performing managed scans with Tenable.sc, some CIS audits require additional patch audits and vulnerability checks. Any additional requirements for completing an audit using the CIS IIS Benchmarks will be included within the audit file description text. In some cases, multiple scans may be required to be performed, as Tenable provides both Level 1 and Level 2 audit checks. Level 1 checks provide minimum setting recommendations, and are generally considered safe to apply to most systems. Level 2 checks include recommendations for complex or highly secure environments, and can lead to reduced functionality of key systems or applications.
When performing audit scans with Tenable.sc, audit files related to the CIS IIS Benchmarks must first be uploaded to Tenable.sc. Next, the appropriate credentials must be added, after which a scan policy can be created. Finally, a scan can be scheduled. As part of the post scan jobs, the 'Auto-Run Reports' can be enabled automatically, running this report on the data collected using the appropriate audit file. Using these benchmarks will help to assess the effectiveness of existing security controls, and provide the critical information needed to improve an organization's security posture.
The reports are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The reports can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The report requirements are:
- Tenable.sc 5.2.0
- Nessus 8.5.1
- CIS Audit Files for Microsoft IIS servers are required, and the files required for each template are listed below with their respective templates.
A key aspect of secure web infrastructures is the hardening of servers using an effective and repeatable way to measure compliance results. With over 200 audit files for CIS and more than 400 audit files overall, Tenable Tenable.sc helps organizations obtain results using the CIS Benchmarks by measuring compliance in real time, providing an accurate assessment of an organization’s security posture. By prioritizing remediation actions for misconfigured systems, the organization can maximize their investment in compliance reporting and system hardening efforts. Tenable.sc delivers comprehensive security solutions that provide continuous visibility and critical context, enabling decisive actions to protect the organization.
Report Templates
CIS IIS Benchmark v1.0 - These report templates provide summaries of all the audit checks for IIS 6.0 benchmark. The templates support systems running IIS 6.0 on Windows XP, Windows 2000, and Windows 2003 operating systems. The benchmark was last updated in 2007, and should only be used on systems that are at the end of their life cycle. The audit files required to support this report template are:
- CIS_v1.0_MS_IIS_6.audit
CIS Microsoft IIS 7 Benchmark v1.8.0 – These report templates provide summaries of all the audit checks for IIS 7.0 and 7.5 benchmarks. The templates support systems running IIS 7.0 and 7.5 on Windows 2008 and Windows 2008 R2 operating systems. The audit files required to support this report template are:
- CIS_v1.8.0_MS_IIS_7_Level_1.audit
- CIS_v1.8.0_MS_IIS_7_Level_2.audit
- CIS_v1.7.1_MS_IIS_7.5_Level_1.audit
- CIS_v1.7.1_MS_IIS_7.5_Level_2.audit
CIS Microsoft IIS 8 Benchmark v1.5.0 - These report templates provide summaries of all the audit checks for CIS Microsoft IIS 8 and 8.5 Benchmark. The templates support systems running IIS 8.0 and 8.5 on Windows Server 2012 and Windows Server 2012 R2 operating systems. The audit files required to support this report template are:
- CIS_v1.5.0_MS_IIS_8_Level_1.audit
- CIS_v1.5.0_MS_IIS_8_Level_2.audit
CIS Microsoft IIS 10 Benchmark v1.0.0 - These report templates provide summaries of all the audit checks for CIS Microsoft IIS 10 Benchmark. The templates support systems running IIS 10 on Windows Server 2016. The audit files required to support this report template are:
- CIS_v1.0.0_MS_IIS_10_Level_1.audit
- CIS_v1.0.0_MS_IIS_10_Level_2.audit