Synopsis
MikroTik WinBox before 3.21 is vulnerable to a path traversal issue that allows an attacker to write files anywhere on the system where WinBox has write privileges.
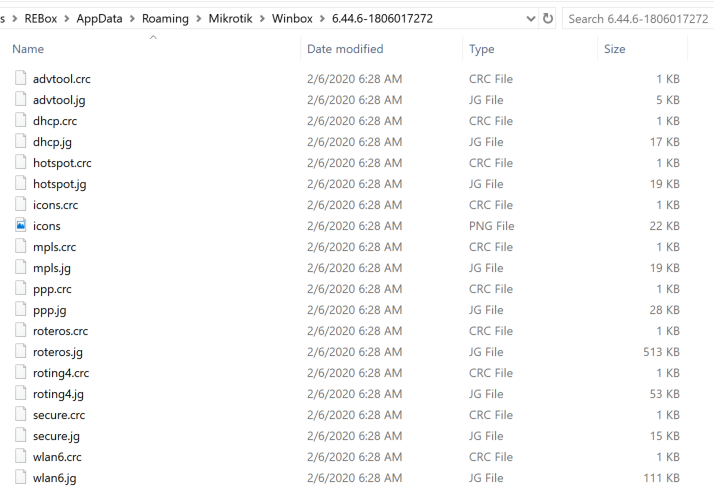
When WinBox connects to a router, it downloads the list file from /home/web/webfig/. This file contains a list of files that WinBox should download in order to obtain package descriptions. WinBox downloads these files and stores them on the client's system within the MikroTik roaming directory: C:\Users\[username]\AppData\Roaming\Mikrotik\Winbox.
The name of the created files come directly from the downloaded list file. For example, this is a line from list:
{ crc: 164562873, size: 1149, name: "advtool.jg", unique: "advtool-fc1932f6809e.jg", version: "6.39.3" }
WinBox will use the name "advtool.jg" as the filename in the roaming directory. However, WinBox doesn't do any type of checking for directory traversal on these files. So if presented with:
{ crc: 164562873, size: 1149, name: "../../../../../../../Users/Public/lol.txt", unique: "advtool-fc1932f6809e.jg", version: "6.39.3" }
Then WinBox would create the file C:\Users\Public\lol.txt and fill it with contents provided by the attacker.
An attacker can exploit this bug by getting a victim to connect to a malicious MikroTik router, a fake router (see our PoC for CVE-2019-3981) , or via a man in the middle attack. The attacker can then perform the downgrade attack described in TRA-2020-01. The client will then try to download the files from the attacker.
A proof of concept has been uploaded to our research GitHub repository. The PoC listens on port 8291. When WinBox connects to it, the script will ignore the ECSRP message so that the client switches to Diffie-Hellman. After the login is complete, the script serves up a malicious list file and eventually writes the file C:\Users\Public\lol.txt with the contents "hello mikrotik".
Solution
Upgrade to Winbox 3.21Disclosure Timeline
All information within TRA advisories is provided “as is”, without warranty of any kind, including the implied warranties of merchantability and fitness for a particular purpose, and with no guarantee of completeness, accuracy, or timeliness. Individuals and organizations are responsible for assessing the impact of any actual or potential security vulnerability.
Tenable takes product security very seriously. If you believe you have found a vulnerability in one of our products, we ask that you please work with us to quickly resolve it in order to protect customers. Tenable believes in responding quickly to such reports, maintaining communication with researchers, and providing a solution in short order.
For more details on submitting vulnerability information, please see our Vulnerability Reporting Guidelines page.
If you have questions or corrections about this advisory, please email [email protected]
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success