by Cody Dumont
May 23, 2022
Exploits leveraged in attacks are imported into various tools and services when the attack is made public. Common exploit frameworks are easy to obtain and are used by security researchers and malicious attackers. Security analysts can effectively reduce risk to the organization by analyzing an exploit’s source tool and the most common targets. This report provides details on exploit frameworks that can be used against the network.
The Cyber Security Framework (CSF) category ID.RA (Risk Assessment) provides guidance to organizations on cyber risk and helps to define recommended actions for the security operations team. The ID.RA-1 category states requirements for the National Institute of Standards and Technology (NIST) 800-53 control CA-8 Penetration Testing. The control states “Penetration testing is a specialized type of assessment conducted on information systems or individual system components to identify vulnerabilities that could be exploited by adversaries.” Some security teams leverage exploitation frameworks such as Core Impact, Canvas or others to help with this control. Tenable.io identifies which vulnerabilities are exploitable by different frameworks.
Risk managers and incident responders are provided detailed information relating to the vulnerabilities exploitable by exploitation frameworks. The report contains details on the host, vulnerability and related information for each exploitation framework. The chapters in the report contain tables reporting vulnerabilities by plugin family, Microsoft bulletins, and CVE. Depending on the reporting metrics used within the organization, risk managers can easily prioritize mitigation efforts. The content in this report helps risk managers understand the level of difficultly needed to exploit the identified vulnerabilities. Vulnerabilities that are not exploitable by a framework may be more difficult to exploit and therefore may have a lesser priority level. Mitigation is still very important, but Tenable recommends prioritizing mitigation for vulnerabilities with exploits that are exploitable via a framework.
Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable.io discovers and analyzes assets continuously to provide an accurate and unified view of an organization’s security posture.
Chapters
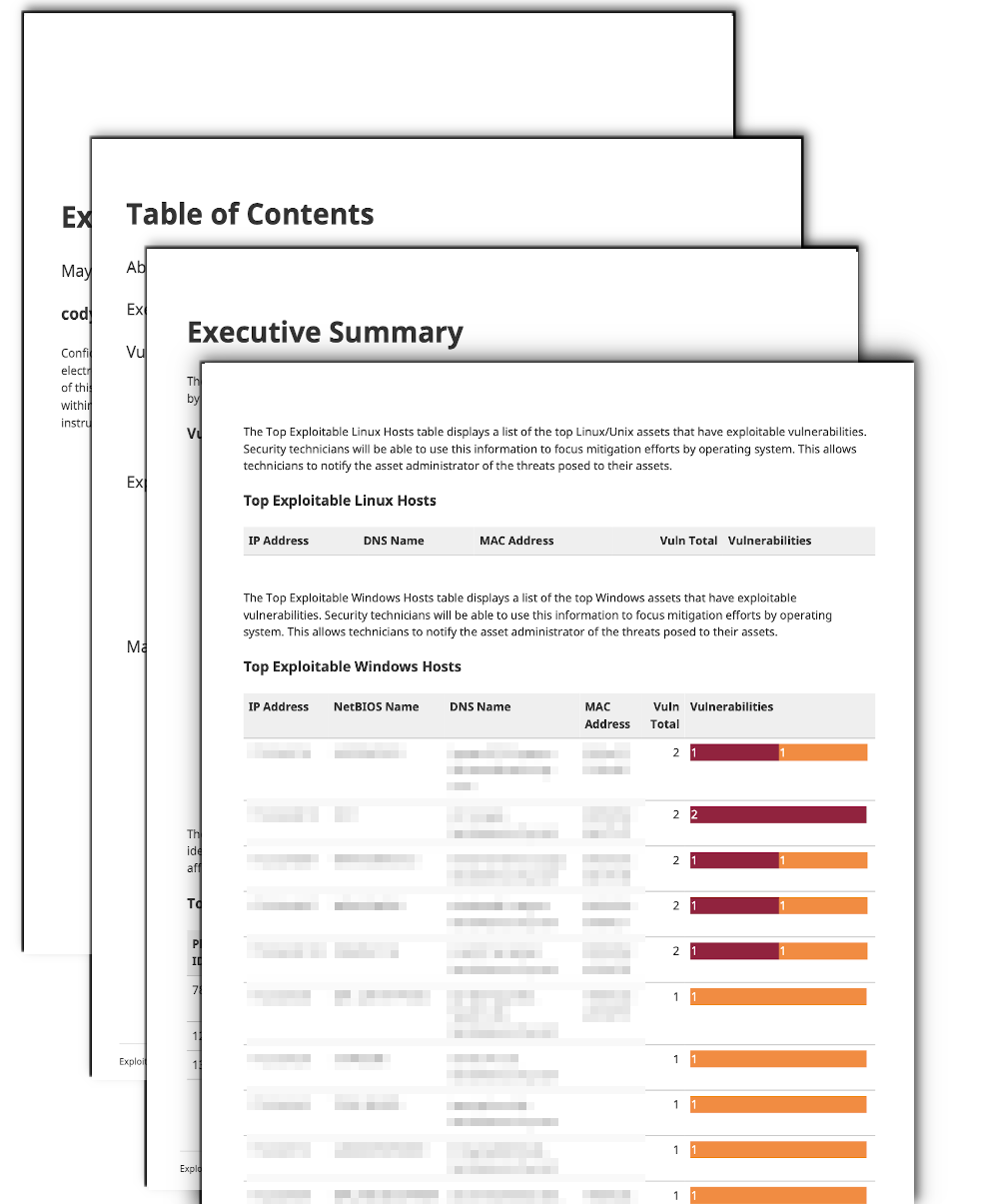
Executive Summary: This chapter provides an overview of the exploitable vulnerabilities in the organization
Bad Autoruns: This chapter is a summary of exploitable vulnerabilities with Bad Autoruns
Canvas: This chapter is a summary of exploitable vulnerabilities with the Canvas exploitation framework
Core Impact: This chapter is a summary of exploitable vulnerabilities with the Core Impact exploitation framework
Elliot: This chapter is a summary of exploitable vulnerabilities with the Elliot exploitation framework
ExploitHub: This chapter is a summary of exploitable vulnerabilities with the ExploitHub exploitation framework
Malware: This chapter is a summary of exploitable vulnerabilities with malware
MetaSploit: This chapter is a summary of exploitable vulnerabilities with the MetaSploit exploitation framework
Exploit Framework Details: This chapter provides detailed information of hosts affected with exploitable vulnerabilities