by Josef Weiss
The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides technical and operational requirements for organizations accepting or processing payment transactions, and for software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies and ongoing processes that protect their payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 4.x. Any organization that handles payment card information must comply with the PCI DSS and must demonstrate compliance annually. Tenable Vulnerability Management is able to help organizations monitor ongoing PCI DSS compliance.
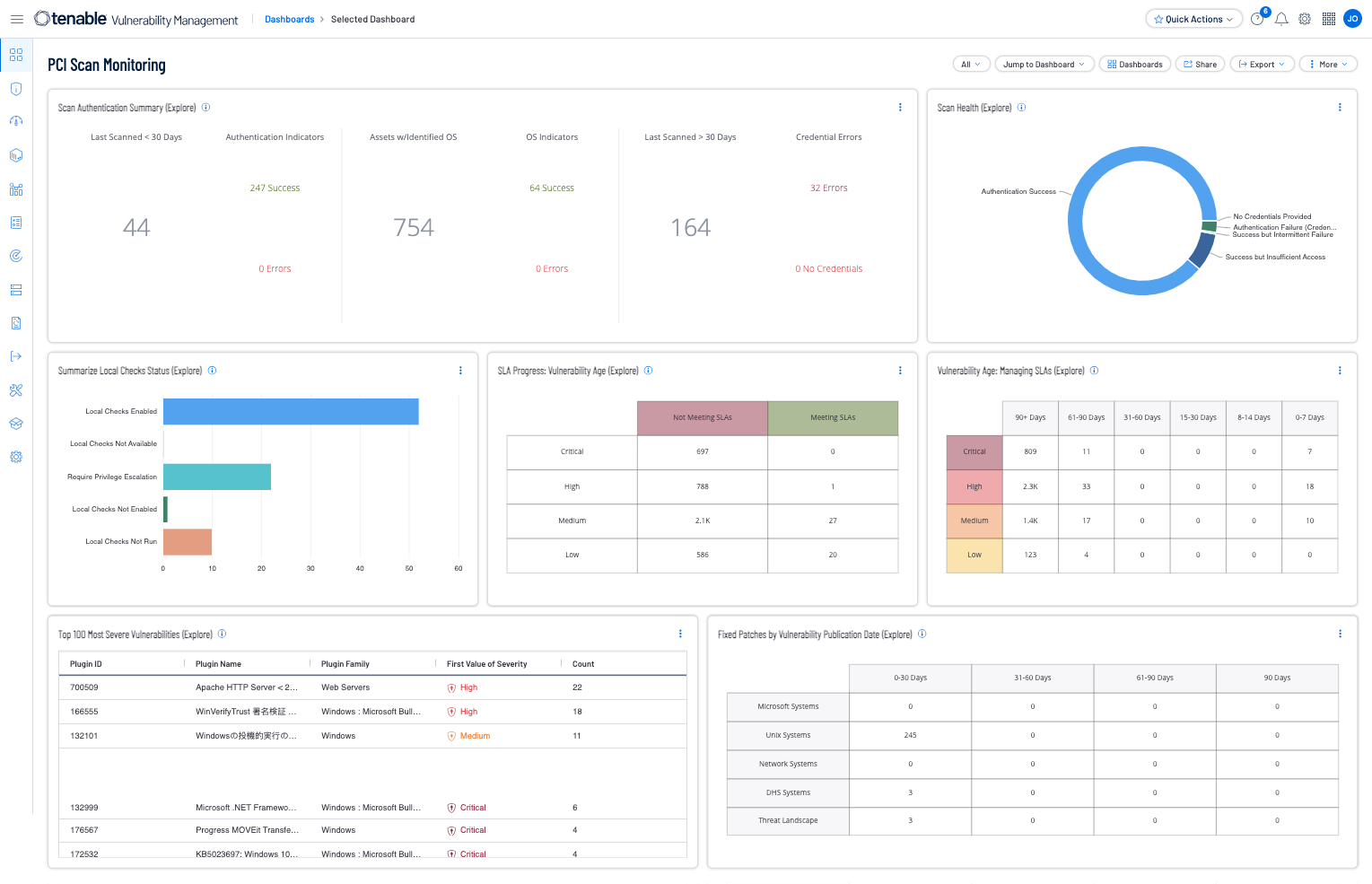
The PCI Scan Monitoring dashboard provides security teams with detailed insight into their organization and vulnerability management posture. Vulnerabilities are filtered by severity and exploitability to identify at-risk hosts. Detailed information about remediation opportunities and risk issues are presented. Indicator matrices alert to the detection of specific exploitable vulnerabilities and patch management details. Nessus scans are monitored for progress and errors, and vulnerability trend data is presented. By effectively monitoring the network for vulnerabilities and remediation options, security teams can better ensure network integrity and security. The widgets in this dashboard are focused on PCI requirement 11.2, which focuses on performing network vulnerability scans. The dashboard covers PCI Requirement 11.3.1.3, which focuses on specific vulnerability scanning requirements.
Organizations can configure repositories or asset lists in order to tailor the focus of the dashboard. After the dashboard is added from the Template Library, the appropriate assets can be specified for each widget on the dashboard. By creating tags and target groups that include all systems in the Cardholder Data Environment (CDE), each widget can be filtered to display results directly related to ongoing PCI security.
Tenable provides several solutions for organizations to better understand vulnerability management. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Vulnerability Management (formerly Tenable.io) discovers and analyzes assets continuously to provide an accurate and unified view of an organization's security posture. The requirements for this report are: Tenable Vulnerability Management.
Widgets:
- Scan Authentication Summary (Explore) - This widget provides a summary of scan health in relation to authentication success and failures.
- Scan Health (Explore) - This widget provides a summary of scan health in relation to authentication success and failures.
- Summarize Local Checks Status (Explore) - This widget provides summaries of local checks status.
- SLA Progress: Vulnerability Age (Explore) - This widget helps organizations manage Service Level Agreements (SLAs) by providing a vulnerability view that is organized by Vulnerability Priority Rating (VPR) Score and Vulnerability Age.
- Vulnerability Age: Managing SLAs (Explore) - This widget provides a view of vulnerabilities based on severity and age.
- Top 100 Most Severe Vulnerabilities (Explore) - This widget displays the top 100 most severe vulnerabilities detected in the environment using the VPR filter for 7.0 - 10.0.
- Fixed Patches by Vulnerability Publication Date (Explore) - This widget displays columns that contain counts of fixed vulnerabilities grouped by the patch publication dates of 0-30, 31-60, 61-90, and more than 90 days ago.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success