Cybersecurity Snapshot: New Guides Offer Best Practices for Preventing Shadow AI and for Deploying Secure Software Updates

Looking for help with shadow AI? Want to boost your software updates’ safety? New publications offer valuable tips. Plus, learn why GenAI and data security have become top drivers of cyber strategies. And get the latest on the top “no-nos” for software security; the EU’s new cyber law; and CISOs’ communications with boards.
Dive into six things that are top of mind for the week ending Oct. 25.
1 - CSA: How to prevent “shadow AI”
As organizations scale up their AI adoption, they must closely track their AI assets to secure them and mitigate their cyber risk. This includes monitoring the usage of unapproved AI tools by employees — an issue known as “shadow AI.”
So how do you identify, manage and prevent shadow AI? You may find useful ideas in the Cloud Security Alliance’s new “AI Organizational Responsibilities: Governance, Risk Management, Compliance and Cultural Aspects” white paper.
The white paper covers shadow AI topics including:
- Creating a comprehensive inventory of AI systems
- Conducting gap analyses to spot discrepancies between approved and actual AI usage
- Implementing ways to detect unauthorized AI wares
- Establishing effective access controls
- Deploying monitoring techniques

“By focusing on these key areas, organizations can significantly reduce the risks associated with shadow AI, ensuring that all AI systems align with organizational policies, security standards, and regulatory requirements,” the white paper reads.
For example, to create an inventory that offers the required visibility into AI assets, the document explains different elements each record should have, such as:
- The asset’s description
- Information about its AI models
- Information about its data sets and data sources
- Information about the tools used for its development and deployment
- Detailed documentation about its lifecycle, regulatory compliance, ethical considerations and adherence to industry standards
- Records of its access control mechanisms
Shadow AI is one of four topics covered in the publication, which also unpacks risk management; governance and compliance; and safety culture and training.
To get more details, read:
- The full “AI Organizational Responsibilities: Governance, Risk Management, Compliance and Cultural Aspects” white paper
- A complementary slide presentation
- The CSA blog “Shadow AI Prevention: Safeguarding Your Organization’s AI Landscape”
For more information about AI security issues, including shadow AI, check out these Tenable blogs:
- “Do You Think You Have No AI Exposures? Think Again”
- “Securing the AI Attack Surface: Separating the Unknown from the Well Understood”
- “Never Trust User Inputs -- And AI Isn't an Exception: A Security-First Approach”
- “6 Best Practices for Implementing AI Securely and Ethically”
- “Compromising Microsoft's AI Healthcare Chatbot Service”
2 - Best practices for secure software updates
The security and reliability of software updates took center stage in July when an errant update caused massive and unprecedented tech outages globally.
To help prevent such episodes, U.S. and Australian cyber agencies have published “Safe Software Deployment: How Software Manufacturers Can Ensure Reliability for Customers.”
“It is critical for all software manufacturers to implement a safe software deployment program supported by verified processes, including robust testing and measurements,” reads the 12-page document.
Although the guide is aimed primarily at commercial software vendors, its recommendations can be useful for any organization with software development teams that deploy updates internally.
The guide outlines key steps for a secure software development process, including planning; development and testing; internal rollout; and controlled rollout. It also addresses errors and emergency protocols.
“A safe software deployment process should be integrated with the organization’s SDLC, quality program, risk tolerance, and understanding of the customer’s environment and operations,” reads the guide, authored by the U.S. Cybersecurity and Infrastructure Security Agency (CISA), the FBI and the Australian Cyber Security Centre.
To get more details, read:
- The “Safe Software Deployment: How Software Manufacturers Can Ensure Reliability for Customers” guide
- The CISA alert “CISA, US, and International Partners Release Joint Guidance to Assist Software Manufacturers with Safe Software Deployment Processes”
For more information about secure software updates:
- “Tenable’s Software Update Process Protects Customers’ Business Continuity with a Safe, Do-No-Harm Design” (Tenable)
- “The critical importance of robust release processes” (Cloud Native Computing Foundation)
- “Software Deployment Security: Risks and Best Practices” (DevOps.com)
- “Software Updates, A Double-Edged Sword for Cybersecurity Professionals” (Infosecurity)
- “DevOps Best Practices for Faster and More Reliable Software Delivery” (DevOps.com)
3 - Report: GenAI, attack variety, data security drive cyber strategies
What issues act as catalysts for organizations’ cybersecurity actions today? Hint: They’re fairly recent concerns. The promise and peril of generative AI ranks first. It’s closely followed by the ever growing variety of cyberattacks; and by the intensifying urgency to protect data.
That’s according to CompTIA’s “State of Cybersecurity 2025” report, based on a survey of almost 1,200 business and IT pros in North America and in parts of Europe and Asia.
These three key factors, along with others like the scale of attacks, play a critical role in how organizations currently outline their cybersecurity game plans.
“Understanding these drivers is essential for organizations to develop proactive and adaptive cybersecurity strategies that address the evolving threat landscape and safeguard their digital assets,” reads a CompTIA blog about the report.
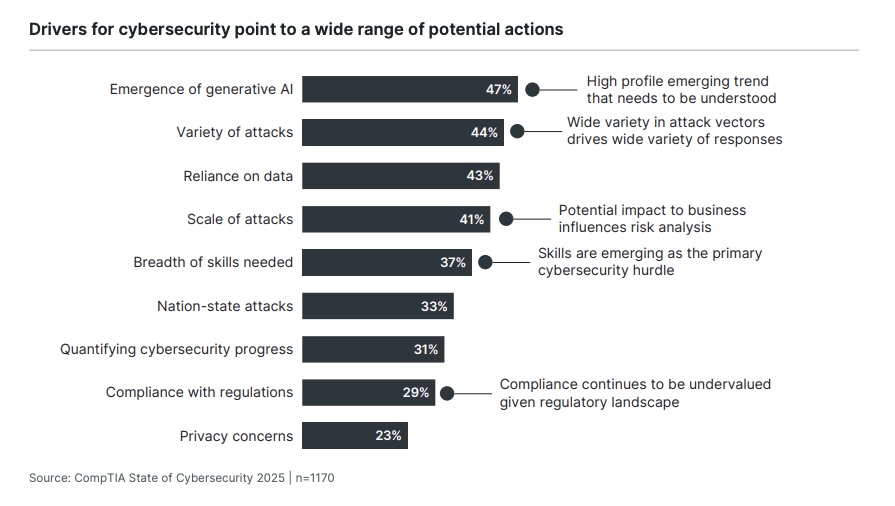
Organizations are eagerly trying to understand both how generative AI can help their cybersecurity programs and how this technology is being used by malicious actors to make cyberattacks harder to detect and prevent.
Meanwhile, concern about data protection has ballooned in the past couple of years. “As organizations become more data-driven, the need to protect sensitive information has never been more crucial,” reads the blog.
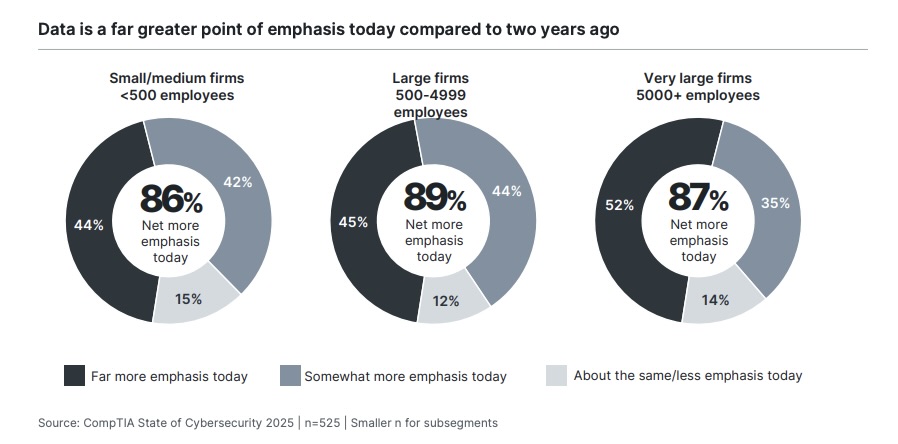
Not only are organizations focused on securing data at rest, in transit and in use, but they’re also creating foundational data-management practices, according to the report.
“The rise of AI has accelerated the need for robust data practices in order to properly train AI algorithms, and the demand for data science continues to be strong as businesses seek competitive differentiation,” the report reads.
To get more details, read:
- The report’s announcement “Cybersecurity success hinges on full organizational support, new CompTIA report asserts”
- CompTIA’s blogs “Today’s top drivers for cybersecurity strategy” and “Cybersecurity’s maturity: CompTIA’s State of Cybersecurity 2025 report”
- The full “State of Cybersecurity 2025” report
For more information about data security posture management (DSPM) and preventing AI-powered attacks, check out these Tenable resources:
- “Harden Your Cloud Security Posture by Protecting Your Cloud Data and AI Resources” (blog)
- “Know Your Exposure: Is Your Cloud Data Secure in the Age of AI?” (on-demand webinar)
- “The Data-Factor: Why Integrating DSPM Is Key to Your CNAPP Strategy” (blog)
- “Mitigating AI-Related Security Risks” (on-demand webinar)
- “Securing the AI Attack Surface: Separating the Unknown from the Well Understood” (blog)
4 - CISA lists software dev practices most harmful for security
Recommended best practices abound in the cybersecurity world. However, CISA and the FBI are taking the opposite tack in their quest to improve the security of software products: They just released a list of the worst security practices that software manufacturers ought to avoid.
Titled “Product Security Bad Practices,” the document groups the “no-nos” into three main categories: product properties; security features; and organizational processes and policies.
“It’s 2024, and basic, preventable software defects continue to enable crippling attacks against hospitals, schools, and other critical infrastructure. This has to stop,” CISA Director Jen Easterly said in a statement.
“These product security bad practices pose unacceptable risks in this day and age, and yet are all too common,” she added.
Here are some of the worst practices detailed in the document, which is part of CISA’s “Secure by Design” effort:
- Using programming languages considered “memory unsafe”
- Including user-provided input in SQL query strings
- Releasing a product with default passwords
- Releasing a product with known and exploited vulnerabilities
- Not using multi-factor authentication
- Failing to disclose vulnerabilities in a timely manner
Although the guidance is aimed primarily at software makers whose products are used by critical infrastructure organizations, the recommendations apply to all software manufacturers.
If you’re interested in sharing your feedback with CISA and the FBI, you can submit comments about the document until December 16, 2024 on the Federal Register.
To get more details, check out:
- CISA’s announcement “CISA and FBI Release Product Security Bad Practices for Public Comment”
- The full document “Product Security Bad Practices”
For more information about how to develop secure software:
- “Tenable Partners with CISA to Enhance Secure By Design Practices” (Tenable)
- “Ensuring Application Security from Design to Operation with DevSecOps” (DevOps.com)
- “What is application security?” (TechTarget)
- “Guidelines for Software Development (Australian Cyber Security Centre)
5 - New EU law focuses on cybersecurity of connected digital products
Makers of digital products — both software and hardware — that directly or indirectly connect to networks and to other devices will have to comply with specific cybersecurity safeguards in the European Union.
A newly adopted law known as the “Cyber Resilience Act” outlines cybersecurity requirements for the design, development, production and lifecycle maintenance of these types of products, including IoT wares such as connected cars.

For example, it specifies a number of “essential cybersecurity requirements” for these products, including that they:
- Aren’t shipped with known exploitable vulnerabilities
- Feature a “secure by default” configuration
- Can fix their vulnerabilities via automatic software updates
- Offer access protection via control mechanisms, such as authentication and identity management
- Protect the data they store, transmit and process using, for example, at-rest and in-transit encryption
“The new regulation aims to fill the gaps, clarify the links, and make the existing cybersecurity legislative framework more coherent, ensuring that products with digital components (...) are made secure throughout the supply chain and throughout their lifecycle,” reads a statement from the EU’s European Council.
The law will “enter into force” after its publication in the EU’s official journal and will apply and be enforceable 36 months later, so most likely in October 2027 or November 2027. However, some of its provisions will be enforceable a year prior.
For more information and analysis about the EU’s Cyber Resilience Act:
- “Cyber Resilience Act Requirements Standards Mapping” (ENISA)
- “The Cyber Resilience Act, an Accidental European Alien Torts Statute?” (Lawfare)
- “EU Cybersecurity Regulation Adopted, Impacts Connected Products” (National Law Review)
- “Open source foundations unite on common standards for EU’s Cyber Resilience Act” (TechCrunch)
- “The Cyber Resilience Act: A New Era for Mobile App Developers” (DevOps.com)
VIDEO
The EU Cyber Resilience Act: A New Era for Business Engagement in Open Source Software (Linux Foundation)
6 - UK cyber agency: CISOs must communicate better with boards
CISOs and boards of directors are struggling to understand each other, and this is increasing their organizations’ cyber risk, new research from the U.K.’s cyber agency has found.
For example, in one alarming finding, 80% of respondents, which included board members, CISOs and other cyber leaders in medium and large enterprises, confessed to being unsure of who is ultimately accountable for cybersecurity in their organizations.
“We found that in many organisations, the CISO (or equivalent role) thought that the Board was accountable, whilst the Board thought it was the CISO,” reads a blog about the research titled “How to talk to board members about cyber.”
As a result, the U.K. National Cyber Security Centre (NCSC) has released new guidance aimed at helping CISOs better communicate with their organizations’ boards titled “Engaging with Boards to improve the management of cyber security risk.”
“Cyber security is a strategic issue, which means you must engage with Boards on their terms and in their language to ensure the cyber risk is understood, managed and mitigated,” the document reads.

Here’s a small sampling of the advice:
- Understand your audience, including who are the board’s members and their areas of expertise; and how the board works, such as its meeting formats and its committees.
- Talk about cybersecurity in terms of risks, and outline these risks concretely and precisely, presenting them in a matter-of-fact way.
- Don’t limit your communication with board members to formal board meetings. Look for opportunities to talk to them individually or in small groups outside of these board meetings.
- Elevate the discussions so that you link cybersecurity with your organization’s business challenges, goals and context.
- Aim to provide a holistic view, and avoid using technical jargon.
- Aim to advise instead of to educate.
- AI
- Cloud
- Exposure Management
- Risk-based Vulnerability Management
- Cloud
- Cybersecurity Snapshot
- DevOps
- Exposure Management
- Federal
- Government
- Risk-based Vulnerability Management

