Cybersecurity Snapshot: RansomHub Group Triggers CISA Warning, While FBI Says North Korean Hackers Are Targeting Crypto Orgs

Cybersecurity teams must beware of RansomHub, a surging RaaS gang. Plus, North Korea has unleashed sophisticated social-engineering schemes against crypto employees. Meanwhile, a new SANS report stresses the importance of protecting ICS and OT systems. And a Tenable poll sheds light on cloud-native VM. And much more!
Dive into six things that are top of mind for the week ending September 6.
1 - CISA: Keep RansomHub RaaS gang on your radar screen
RansomHub, a relatively new ransomware group, has become a serious threat as its successful ransomware-as-a-service (RaaS) model increasingly lures prominent affiliates away from competitors like LockBit.
That’s the warning from CISA, which urges cyber teams to protect their organizations by keeping software updated, adopting phishing-resistant multi-factor authentication and training employees to recognize phishing attacks.
In an advisory titled “#StopRansomware: RansomHub Ransomware,” CISA details the RaaS gang’s tactics, techniques and procedures, as well as its indicators of compromise, and offers mitigation recommendations.

RansomHub and its affiliates have successfully attacked at least 210 organizations from a wide variety of industries, including from multiple critical infrastructure sectors.
Highlights from the advisory include:
- RansomHub affiliates use double extortion, meaning they encrypt victims’ systems and exfiltrate their data.
- Preferred initial-access targets include internet-exposed systems and endpoints, while its go-to attack methods are phishing emails, known-vulnerability exploitation and password spraying.
- These known vulnerabilities have been exploited: CVE-2023-3519, CVE-2023-27997, CVE-2023-46604, CVE-2023-22515, CVE-2023-46747, CVE-2023-48788, CVE-2017-0144, CVE-2020-1472 and CVE-2020-0787.
Recommended mitigation measures include:
- Adopt a recovery plan for storing critical data in locations that are physically separate, segmented and secure. Back up data offline and encrypt it.
- Enforce strong-password requirements.
- Maintain all operating systems, software and firmware updated.
- Protect administrator accounts with phishing-resistant MFA, least-privilege principles and time-based access, like the just-in-time access method.
- Segment networks and monitor them for unusual and suspicious activity.
- Check for unrecognized accounts in domain controllers, servers, workstations and directories.
Previously known as Cyclops and Knight, RansomHub was launched in February of this year and ranked as the most active ransomware group in July with 11% of all attacks, according to NCC Group.
The FBI, the Multi-State Information Sharing and Analysis Center (MS-ISAC) and the Department of Health and Human Services (HHS) partnered with CISA on this advisory.
For more information about ransomware trends and security best practices:
- “Ransomware Is ‘More Brutal’ Than Ever in 2024” (Wired)
- “How Can I Protect Against Ransomware?” (CISA)
- “How to prevent ransomware in 6 steps” (TechTarget)
- “Steps to Help Prevent & Limit the Impact of Ransomware” (Center for Internet Security)
- “Ransomware: How to prevent and recover” (Canadian Centre for Cyber Security)
2 - FBI: North Korean hackers go after crypto players
Using intricate, persistent and stealthy social-engineering schemes, North Korea’s government is targeting staffers at crypto organizations to steal cryptocurrency by breaching their networks using malware.
Specifically, hackers acting on behalf of North Korea’s government have their sights set on organizations that offer cryptocurrency exchange-traded funds (ETFs) and other crypto-based financial products.
That’s according to the FBI, which this week issued an alert for companies in the cryptocurrency sector titled “North Korea Aggressively Targeting Crypto Industry with Well-Disguised Social Engineering Attacks.”
“North Korea employs sophisticated tactics to steal cryptocurrency funds and is a persistent threat to organizations with access to large quantities of cryptocurrency-related assets or products,” reads the FBI alert.

Tactics employed by these North Korean hackers include:
- Conducting thorough and detailed research on employees of the crypto organizations they intend to target
- Creating elaborate fake offers such as employment and investment opportunities that are tailored for each targeted individual
- Interacting extensively one-on-one with the victims, often impersonating real people, such as recruiters
- Requesting to:
- Execute code or download apps on company-owned devices
- Conduct “pre-employment” technical tests or exercises involving the execution of packages and scripts
- Run a script in order to enable voice calls or video meetings
Among the FBI’s recommended mitigations are:
- Develop methods to verify a contact’s identity.
- Don’t keep crypto-wallet information, such as logins and passwords, in devices connected to the internet.
- Decline to take pre-employment tests or to execute code on company-owned devices.
- Conduct multiple authentication checks and require approvals from unconnected networks before carrying out financial transactions.
For more information about crypto hacking trends:
- “Crypto hacking thefts double to $1.4 bln in first half of 2024” (Reuters)
- “Can Crypto Be Hacked?” (Investopedia)
- “2024 Crypto Crime Mid-year Update Part 1 and Part 2” (Chainalysis)
- “The 6 biggest crypto heists of all time” (Quartz)
- “Indian crypto platform WazirX confirms $230 million stolen during cyberattack” (The Record)
3 - Tenable surveys webinar attendees on cloud-native VM
During our recent webinar “A Cyber Pro's Guide to Cloud-Native Vulnerability Management,” we polled attendees about issues related to cloud VM and cloud-native technologies. See what they said about their cloud-native application challenges and cloud VM strategies!
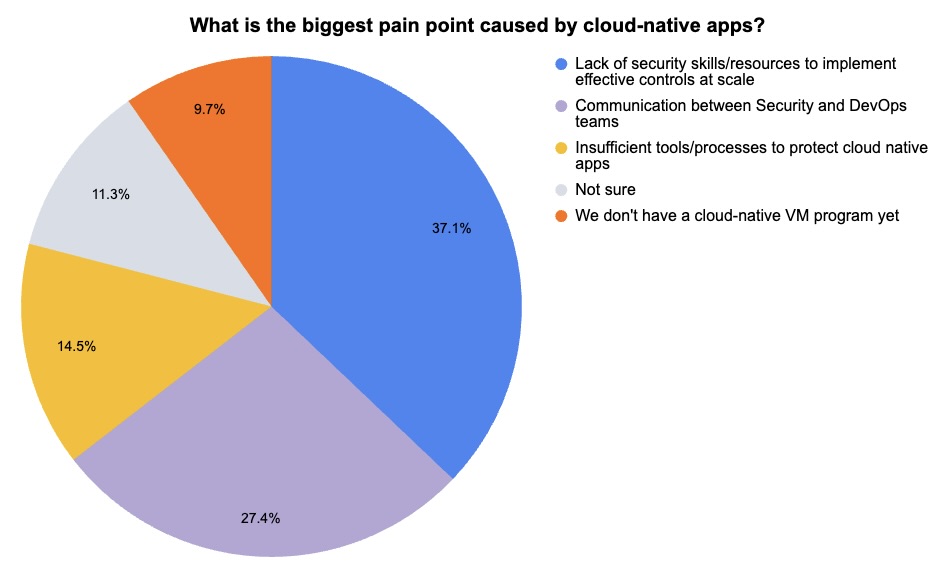
(62 webinar attendees polled by Tenable, August 2024)
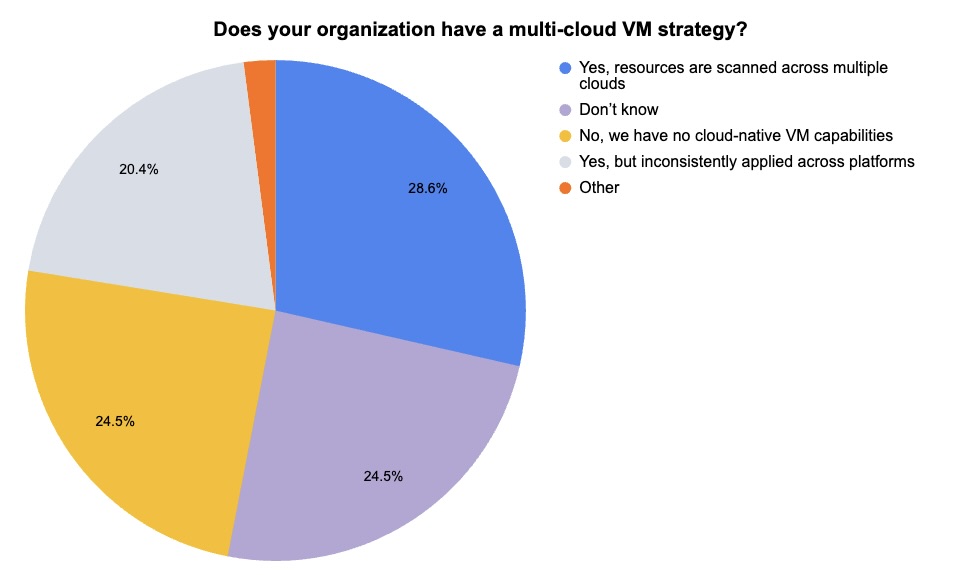
(49 webinar attendees polled by Tenable, August 2024)
Want to learn more about the benefits of agentless cloud security and about extending your VM strategy to the cloud? Watch the on-demand webinar “A Cyber Pro's Guide to Cloud-Native Vulnerability Management” today.
4 - SANS: Businesses can’t ignore security of ICS and OT
Looking for insights and best practices to boost the cybersecurity of your industrial control systems (ICS) and operational technology systems (OT)? You might want to check out SANS Institute’s new guide "ICS Is the Business: Why Securing ICS/OT Environments Is Business-Critical in 2024."
The guide stresses that protecting ICS and OT systems is essential for business success and that to secure ICS and OT systems you can’t use the same strategy, processes and tools you employ to protect the IT environment.
“The steps outlined here are essential for ensuring that our industrial systems continue to operate safely and reliably,” author Dean Parsons, a SANS Certified Instructor, said in a statement.
Topics covered in the paper include:
- An overview of the top threats impacting ICS and OT systems, including targeted, tailored strikes against these environments; ransomware attacks; supply chain breaches; and attacks that originate in the IT network.
- The differences between IT and ICS/OT environments, and why they require a different security approach.
- Five critical cybersecurity controls for ICS/OT:
- ICS-specific incident response
- Network architecture that supports defensible controls, like segmentation and log collection
- ICS network visibility and monitoring
- ICS secure remote access
- Risk-based ICS vulnerability management
- How to use AI to bolster ICS/OT security.
- The ways in which CISOs can advance their organizations’ ICS/OT security maturity.
For more information about OT security, check out these Tenable resources:
- “Unlock Advanced IoT Visibility in your OT Environment Security” (on-demand webinar)
- “How To Secure All of Your Assets - IT, OT and IoT - With an Exposure Management Platform” (blog)
- “Securing The Manufacturing Shop Floor” (white paper)
- “Fortifying Your OT Environment: Vulnerability and Risk Mitigation Strategies” (on-demand webinar)
- “CISA Finding: 90% of Initial Access to Critical Infrastructure Is Gained Via Identity Compromise. What Can You Do About It?” (blog)
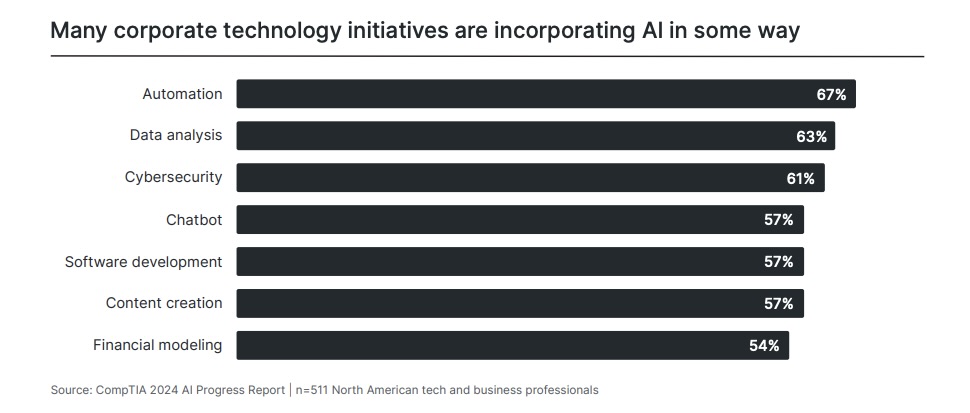
5 - Cybersecurity among top techs getting an AI boost
Cybersecurity ranks high among the technologies into which organizations are integrating AI in order to beef up their tech stacks’ capabilities and improve IT productivity.
That’s according to CompTIA’s “Building AI Strategy” report, based on a survey of 511 tech and business pros in North America.
When respondents were asked which of their tech initiatives are incorporating AI, cybersecurity came in third, mentioned by 61%, behind automation (67%) and data analysis (63%).
“In these (three) cases, AI can understand a wide variety of inputs related to the problem at hand, then provide various forms of assistance, such as direct automation of certain tasks, suggestions of patterns found in data, or predictions of cyber attacks,” the report reads.
Cybersecurity also made the list of respondents’ main concerns related to their use of AI in technology, ranking third. The top concern was finding the right interaction balance between AI tools and employees, followed by infrastructure costs for AI.
For more information about the intersection of AI and cybersecurity, check out these Tenable blogs:
- “How to Discover, Analyze and Respond to Threats Faster with Generative AI”
- “Securing the AI Attack Surface: Separating the Unknown from the Well Understood”
- “Never Trust User Inputs -- And AI Isn't an Exception: A Security-First Approach”
- “Do You Think You Have No AI Exposures? Think Again”
- “AI Is About To Take Cybersecurity By Storm: Here's What You Can Expect”
6 - U.S. government wants to boost security of internet routing
The technology that underpins the internet’s traffic routing is insecure – a dangerous weak link that cyberattackers are increasingly targeting and that represents a global cyber risk.
So said the White House, which is urging a variety of players, including government agencies, internet service providers, academia, mobile operators and cloud providers, to help address the problem.
The report “Roadmap To Enhancing Internet Routing Security” by the Office of the National Cyber Director was released this week and aims to foster the adoption of technologies that can make the ubiquitous Border Gateway Protocol (BGP) more secure.
“As initially designed and commonly operating today, BGP does not provide adequate security and resilience features for the risks we currently face,” the report reads.
For example, BGP is unable to determine if messages exchanged between neighboring networks are authentic, nor can it verify that information from remote networks is legit. Over the past two decades, BGP’s design vulnerabilities have led to serious misconfiguration accidents, and opened the door for a variety of cyberattacks.
The good news is that initial techniques to boost BGP’s security and resilience have been introduced and standardized, and are being deployed, specifically security mechanisms based on Resource Public Key Infrastructure (RPKI), according to the document.
“This roadmap provides recommendations and guidance necessary to increase the adoption of these initial BGP security technologies across all network operators in the Internet ecosystem,” the report reads.
- Cloud
- Cloud
- Cybersecurity Snapshot
- Exposure Management
- Federal
- Government
- Risk-based Vulnerability Management
- SANS

