Study: Tenable Offers Fastest, Broadest Coverage of CISA's KEV Catalog

Tenable ranked first in multiple vulnerability management categories, including the most comprehensive coverage and quickest detection of CISA's Known Exploited Vulnerabilities, according to a Miercom report commissioned by Tenable.
Tenable leads in vulnerability management, topping two other vendors in key criteria, including comprehensiveness and speed of coverage for the Known Exploited Vulnerabilities (KEV) catalog from the U.S. Cybersecurity and Infrastructure Security Agency (CISA). That’s according to the “Vulnerability Management Competitive Assessment” report, published this month by product testing company Miercom and commissioned by Tenable.
Because it lists known vulnerabilities that have been exploited in the wild, the KEV catalog helps security teams prioritize which risks to fix first so that they mitigate the greatest threats to their organizations. In 2022 alone, more than 25,000 new Common Vulnerabilities and Exposures (CVEs) were disclosed.
The report also ranked Tenable first in these other categories:
- Broadest coverage of CVEs in general
- Broadest coverage of CVEs for the top 24 technology vendors
- Broadest coverage of the Center for Internet Security’s CIS Benchmarks configuration recommendations
“We concluded that Tenable Vulnerability Management remains the leader in vulnerability management,” reads the report from Miercom, which has provided product testing for more than 30 years.
The importance of detecting KEVs quickly and accurately
Because most organizations struggle with the staggering amount of risks present in their IT infrastructure, the KEV catalog is an invaluable tool for prioritizing risk remediation, so it’s critical for security teams to be able to detect these issues and to do it quickly.
As Miercom’s white paper shows, Tenable offers the broadest coverage of the KEV catalog and it also updates the KEV coverage of its VM products – Tenable Nessus, Tenable Security Center and Tenable Vulnerability Management – more quickly than its competitors. As such, these Tenable products allow you to meet policy requirements around CISA KEV remediation if your organization has such requirements, and they also help you use KEV catalog data as an additional prioritization metric and data point when figuring out what to fix first.
At Tenable, our goal is to help our customers determine their cyber exposure gap as accurately and quickly as possible. To achieve this goal, we have research teams spread out across the globe so we can provide precise and prompt coverage for new threats as they are discovered. Tenable monitors and tracks additions to the CISA KEV catalog on a daily basis and prioritizes developing new detections where they do not already exist.
Scanning for the CISA KEVs
In general, the default configurations of Tenable scan policies will automatically detect most of the CISA KEVs (and newly added ones) with no changes necessary. However, there are a few that, due to the type and accuracy of detection, may require minor modifications . Review our blogs “CISA Directive 22-01: How Tenable Can Help You Find and Fix Known Exploited Vulnerabilities” and “How to Perform Efficient Vulnerability Assessments with Tenable” for more information and technical documentation.
Finding the CISA KEVs in your scan results
Tenable Nessus Essentials, Professional or Expert
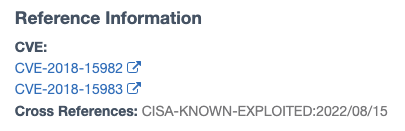
Tenable Nessus customers can filter on a CVE in any completed scan result. Reference information, including when the CVE is “due” for remediation by CISA as referenced in the catalog, is visible in the vulnerability detail view in the bottom right. (For example, Federal Civilian Executive Branch agencies from the U.S. government are required to remediate KEVs within a defined timeframe.)
Tenable Security Center (5.20 and above)
Tenable Security Center customers can use the “Cross References” filters to search automatically for plugins containing CVEs referenced in the KEV catalog.
1. Go to the “Analysis-Vulnerabilities” view and add the “Cross References” filter if not already visible.
2. Type in :
CISA-KNOWN-EXPLOITED|*
(This will give you all plugins that are in your environment that are tracked in the catalog)
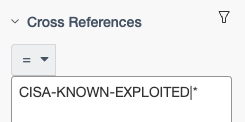
3. When you select the “Vulnerability Detail List” view, you can see the CISA reference with the date in the bottom right:
Other filter examples:
- CISA-KNOWN-EXPLOITED|2023/10/25
(KEV Findings due on October 25, 2023)
- CISA-KNOWN-EXPLOITED|2023/*
(KEV Findings due in 2023)
- CISA-KNOWN-EXPLOITED|2023/23/*
(KEV Findings due in October, 2023)
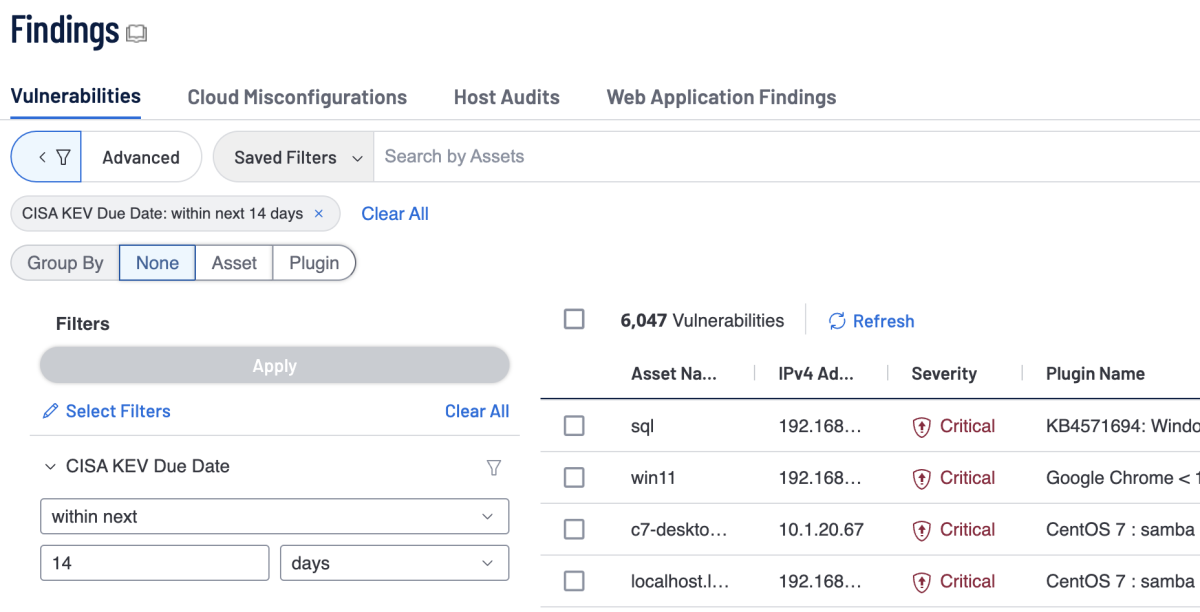
Tenable Vulnerability Management
Tenable Vulnerability Management customers can use the CISA KEV “Due Date” filter in “Explore - Findings” to search automatically for findings containing CVEs referenced in the KEV catalog. Using relative date filters they can also filter for past and future due dates. This filter can also be used in widgets for Dashboards or Reports.
Conclusion
Tenable covers more vulnerabilities and releases detections faster than our competition for vulnerabilities tracked by CISA in its KEV Catalog. All customers receive detections as they’re announced and released as part of their daily plugin updates. In addition, Tenable Security Center and Tenable Vulnerability Management customers have supplementary capabilities to track and measure mitigation of the vulnerabilities in the KEV catalog.
Learn more:
- Known Exploited Vulnerabilities Catalog (CISA)
- Vulnerability Management Competitive Assessment (Miercom white paper)
- CISA Directive 22-01: How Tenable Can Help You Find and Fix Known Exploited Vulnerabilities (blog)
- How to Perform Efficient Vulnerability Assessments with Tenable (blog)
- Nessus - Search and Filter Results (documentation)
- How to filter results based on a search against the cross reference information in a vulnerability (knowledge base article)
- Risk-based Vulnerability Management
- Vulnerability Management
- Nessus
- Risk-based Vulnerability Management
- Vulnerability Management

