CVE-2020-0601: NSA Reported Spoofing Vulnerability in Windows CryptoAPI

Microsoft kicks off the first Patch Tuesday of 2020 with the disclosure of CVE-2020-0601, a highly critical flaw in the cryptographic library for Windows.
UPDATE 01/16/2020: This blog post has been updated to reflect the availability of proof-of-concept code for CVE-2020-0601, which is being referred to as CurveBall or Chain of Fools.
Background
On January 14, Microsoft released its first Patch Tuesday of 2020, which contains an update for a critical vulnerability in the cryptographic library used in newer versions of Windows, including Windows 10 and Windows Server 2016/2019. CVE-2020-0601 was disclosed to Microsoft by the National Security Agency (NSA) via Microsoft’s Coordinated Vulnerability Disclosure process.
Widespread speculation about a severe vulnerability in Microsoft Windows began to circulate on January 13 when Will Dormann, senior vulnerability analyst with the CERT Coordination Center (CERT/CC), hinted in a tweet that people should “pay very close attention” to the updates in Microsoft’s January 2020 Patch Tuesday.
I get the impression that people should perhaps pay very close attention to installing tomorrow's Microsoft Patch Tuesday updates in a timely manner. Even more so than others.
I don't know… just call it a hunch?
¯_(ツ)_/¯— Will Dormann (@wdormann) January 13, 2020
Shortly thereafter, investigative journalist Brian Krebs tweeted a warning about “an extraordinarily scary flaw in all Windows versions,” specifically mentioning the flaw was in a core cryptographic component.
Sources say Microsoft on Tuesday will fix an extraordinarily scary flaw in all Windows versions, in a core cryptographic component that could be abused to spoof the source of digitally signed software. Apparently DoD & a few others got an advance patch https://t.co/V6PByhjTNR
— briankrebs (@briankrebs) January 13, 2020
Krebs later released a blog post with additional details on the event. According to Krebs, the flaw exists in crypt32.dll, the Microsoft Cryptographic Application Programming Interface (CryptoAPI) used for certificate and cryptographic messaging functions. The post also indicates that branches of the U.S. military and other high-value customers received advance notice and patches from Microsoft under non-disclosure agreements (NDAs).
On January 14, Krebs tweeted more information after a media call with the NSA’s director of cybersecurity, Anne Neuberger. According to the tweets, the critical cryptographic vulnerability was discovered by the NSA and reported to Microsoft. The tweet further explains that the vulnerability exists in Windows 10 and Windows Server 2016 and the flaw “makes trust vulnerable.”
NSA's dir. of cybersecurity Anne Neuberger says the critical cryptographic vulnerability resides in Windows 10 and Windows Server 2016, and that the concern about this particular flaw is that it "makes trust vulnerable."
— briankrebs (@briankrebs) January 14, 2020
Analysis
CVE-2020-0601 is a spoofing vulnerability in crypt32.dll, a core cryptographic module in Microsoft Windows responsible for implementing certificate and cryptographic messaging functions in Microsoft’s CryptoAPI.
According to the NSA (credited with the discovery of this vulnerability), successful exploitation of this vulnerability would allow attackers to deliver malicious code that appears to be from a trusted entity. The analysis notes some examples of where validation of trust would be impacted:
- HTTPs connections
- Signed files and emails
- Signed executable code launched as user-mode processes
Because CVE-2020-0601 reportedly bypasses Windows’ capability to verify cryptographic trust, an attacker could pass malicious applications off as legitimate, trusted code, putting Windows hosts at risk. An attacker would need to compromise a system in another fashion to deploy malware that exploits this vulnerability. They would likely either use common phishing tactics to trick a trusted user into interacting with a malicious application or use a man-in-the-middle attack through another compromised device in the environment to spoof an intercepted update and replace it with malware.
Proof of concept
At the time this blog post was published, no proof of concept (PoC) had been released for this vulnerability. However, since details about the vulnerability became public on January 14, security researchers have published tweets hinting they’ve developed working PoCs.
CVE-2020-0601 pic.twitter.com/8tJsJqvnHj
— Saleem Rashid (@saleemrash1d) January 15, 2020
On January 15, a PoC from Danish security researcher ollypwn, who calls the vulnerability CurveBall, was published to GitHub. It was followed by a PoC from security researchers Sylvain Pelissier and Yolan Romailler of Kudelski Security, who call the vulnerability Chain of Fools, which was a name given by Kenneth White, security principal at MongoDB. Earlier today, security researcher Saleem Rashid published a PoC to GitHub, which he calls BADECPARAMS, and can be used to generate “a root certificate authority that exploits the vulnerability, then issues Authenticode and TLS certificates.”
Vendor response
Microsoft has stated that they’ve seen no active exploitation of this vulnerability so far. However, the vulnerability is labeled as ‘Exploitation More Likely’ in Microsoft’s Security Advisory.
Solution
Microsoft has released software updates to address CVE-2020-0601. If patching the vulnerability enterprisewide is not possible, the NSA has advised “prioritizing patching systems that perform Transport Layer Security validation, or host critical infrastructure like domain controllers, Domain Name System servers, Virtual Private Network servers, etcetera.” Additionally, Tenable suggests patching endpoints directly exposed to the internet or systems regularly used by privileged users.
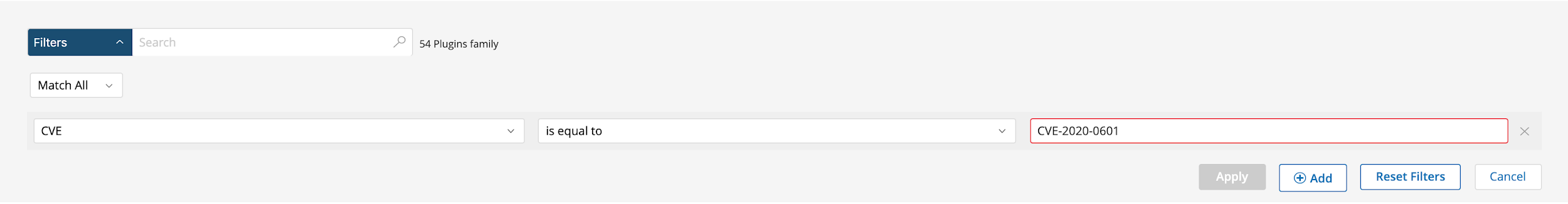
Users can create scans that focus specifically on this vulnerability. From a new advanced scan, in the plugins tab, set an advanced filter for CVE is equal to CVE-2020-0601.
Identifying affected systems
A list of Tenable plugins to identify CVE-2020-0601 will appear here as they’re released.
A list of all the plugins released for Tenable’s January 2020 Patch Tuesday update can be found here.
Get more information
- Microsoft advisory for CVE-2020-0601
- Microsoft blog post on CVE-2020-0601
- National Security Agency bulletin on CVE-2020-0601
- Tenable webinar on the Microsoft CryptoAPI
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management

