Microsoft’s November 2024 Patch Tuesday Addresses 87 CVEs (CVE-2024-43451, CVE-2024-49039)
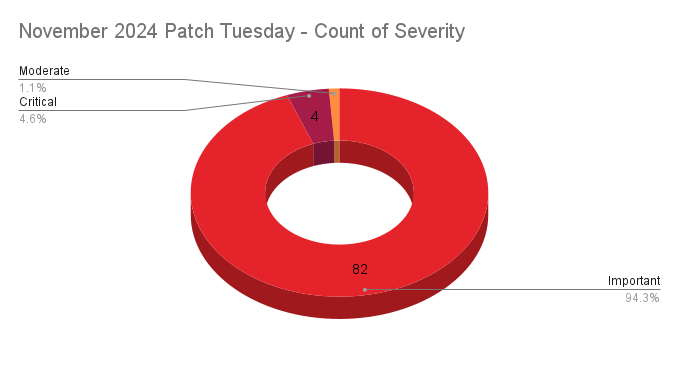
- 4Critical
- 82Important
- 1Moderate
- 0Low
Microsoft addresses 87 CVEs and one advisory (ADV240001) in its November 2024 Patch Tuesday release, with four critical vulnerabilities and four zero-day vulnerabilities, including two that were exploited in the wild.
Microsoft patched 87 CVEs in its November 2024 Patch Tuesday release, with four rated critical, 82 rated important and one rated moderate.
This month’s update includes patches for:
- .NET and Visual Studio
- Airlift.microsoft.com
- Azure CycleCloud
- Azure Database for PostgreSQL
- LightGBM
- Microsoft Exchange Server
- Microsoft Graphics Component
- Microsoft Office Excel
- Microsoft Office Word
- Microsoft PC Manager
- Microsoft Virtual Hard Drive
- Microsoft Windows DNS
- Role: Windows Hyper-V
- SQL Server
- TorchGeo
- Visual Studio
- Visual Studio Code
- Windows Active Directory Certificate Services
- Windows CSC Service
- Windows DWM Core Library
- Windows Defender Application Control (WDAC)
- Windows Kerberos
- Windows Kernel
- Windows NT OS Kernel
- Windows NTLM
- Windows Package Library Manager
- Windows Registry
- Windows SMB
- Windows SMBv3 Client/Server
- Windows Secure Kernel Mode
- Windows Task Scheduler
- Windows Telephony Service
- Windows USB Video Driver
- Windows Update Stack
- Windows VMSwitch
- Windows Win32 Kernel Subsystem
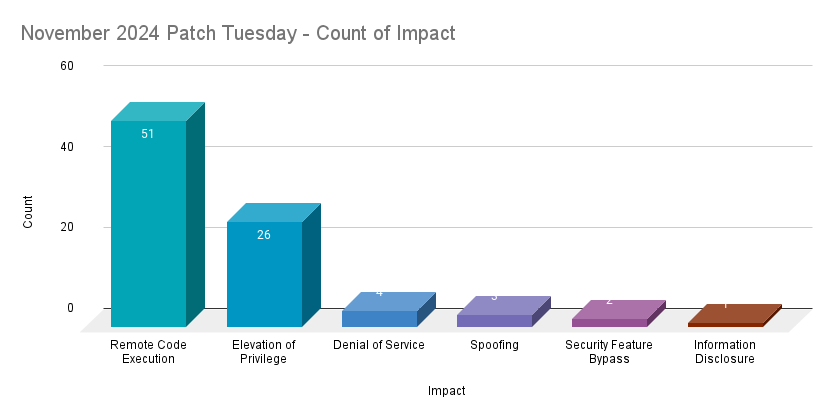
Remote code execution (RCE) vulnerabilities accounted for 58.6% of the vulnerabilities patched this month, followed by elevation of privilege (EoP) vulnerabilities at 29.9%.
CVE-2024-43451 | NTLM Hash Disclosure Spoofing Vulnerability
CVE-2024-43451 is a NTLM hash spoofing vulnerability in Microsoft Windows. It was assigned a CVSSv3 score of 6.5 and is rated as important. An attacker could exploit this flaw by convincing a user to open a specially crafted file. Successful exploitation would lead to the unauthorized disclosure of a user’s NTLMv2 hash, which an attacker could then use to authenticate to the system as the user. According to Microsoft, CVE-2024-43451 was exploited in the wild as a zero-day. No further details about this vulnerability were available at the time this blog post was published.
This is the second NTLM spoofing vulnerability disclosed in 2024. Microsoft patched CVE-2024-30081 in its July Patch Tuesday release.
CVE-2024-49039 | Windows Task Scheduler Elevation of Privilege Vulnerability
CVE-2024-49039 is an EoP vulnerability in the Microsoft Windows Task Scheduler. It was assigned a CVSSv3 score of 8.8 and is rated as important. An attacker with local access to a vulnerable system could exploit this vulnerability by running a specially crafted application. Successful exploitation would allow an attacker to access resources that would otherwise be unavailable to them as well as execute code, such as remote procedure call (RPC) functions.
According to Microsoft, CVE-2024-49039 was exploited in the wild as a zero-day. It was disclosed to Microsoft by an anonymous researcher along with Vlad Stolyarov and Bahare Sabouri of Google's Threat Analysis Group. At the time this blog post was published, no further details about in-the-wild exploitation were available.
CVE-2024-49019 | Active Directory Certificate Services Elevation of Privilege Vulnerability
CVE-2024-49019 is an EoP vulnerability affecting Active Directory Certificate Services. It was assigned a CVSSv3 score of 7.8 and is rated as important. It was publicly disclosed prior to a patch being made available. According to Microsoft, successful exploitation would allow an attacker to gain administrator privileges. The advisory notes that “certificates created using a version 1 certificate template with Source of subject name set to ‘Supplied in the request’” are potentially impacted if the template has not been secured according to best practices. This vulnerability is assessed as “Exploitation More Likely” according to Microsoft’s Exploitability Index. Microsoft’s advisory also includes several mitigation steps for securing certificate templates which we highly recommend reviewing.
CVE-2024-49040 | Microsoft Exchange Server Spoofing Vulnerability
CVE-2024-49040 is a spoofing vulnerability affecting Microsoft Exchange Server 2016 and 2019. It was assigned a CVSSv3 score of 7.5 and rated as important. According to Microsoft, this vulnerability was publicly disclosed prior to a patch being made available. After applying the update, administrators should review the support article Exchange Server non-RFC compliant P2 FROM header detection. The supplemental guide notes that as part of a “secure by default” approach, the Exchange Server update for November will flag suspicious emails which may contain “malicious patterns in the P2 FROM header.” While this feature can be disabled, Microsoft strongly recommends leaving it enabled to provide further protection from phishing attempts and malicious emails.
CVE-2024-43639 | Windows Kerberos Remote Code Execution Vulnerability
CVE-2024-43639 is a critical RCE vulnerability affecting Windows Kerberos, an authentication protocol designed to verify user or host identities. It was assigned a CVSSv3 score of 9.8 and is rated as “Exploitation Less Likely.”
To exploit this vulnerability, an unauthenticated attacker needs to leverage a cryptographic protocol vulnerability in order to achieve RCE. No further details were provided by Microsoft about this vulnerability at the time this blog was published.
29 CVEs | SQL Server Native Client Remote Code Execution Vulnerability
This month's release included 29 CVEs for RCEs affecting SQL Server Native Client. All of these CVEs received CVSSv3 scores of 8.8 and were rated as “Exploitation Less Likely.” Successful exploitation of these vulnerabilities can be achieved by convincing an authenticated user into connecting to a malicious SQL server database using an affected driver. A full list of the CVEs are included in the table below.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2024-38255 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-43459 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-43462 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48993 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48994 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48995 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48996 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48997 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48998 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-48999 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49000 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49001 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49002 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49003 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49004 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49005 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49006 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49007 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49008 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49009 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49010 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49011 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49012 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49013 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49014 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49015 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49016 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49017 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
| CVE-2024-49018 | SQL Server Native Client Remote Code Execution Vulnerability | 8.8 |
CVE-2024-43602 | Azure CycleCloud Remote Code Execution Vulnerability
CVE-2024-43602 is a RCE vulnerability in Microsoft’s Azure CycleCloud, a tool that helps in managing and orchestrating High Performance Computing (HPC) environments in Azure. This flaw received the highest CVSSv3 score of the month, a 9.9 and was rated as important. A user with basic permissions could exploit CVE-2024-43602 by sending specially crafted requests to a vulnerable AzureCloud CycleCloud cluster to modify its configuration. Successful exploitation would result in the user gaining root permissions, which could then be used to execute commands on any cluster in the Azure CycleCloud as well as steal admin credentials.
Tenable Solutions
A list of all the plugins released for Microsoft’s November 2024 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.
Get more information
- Microsoft's November 2024 Security Updates
- Tenable plugins for Microsoft November 2024 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
- Exposure Management
- Vulnerability Management
- Exposure Management
- Vulnerability Management

